Operations | Monitoring | ITSM | DevOps | Cloud
Latest News
Protect your Elasticsearch deployments against attacks like "meow bot" - for free
The issue of unsecured databases is growing. In 2019, 17 percent of all data breaches were caused by human error — twice as many as just a year before. And the IBM/Ponemon 2019 report found that the estimated probability of a company having repeated data breaches within two years grew by 31 percent between 2014 and 2019. Why is this happening?
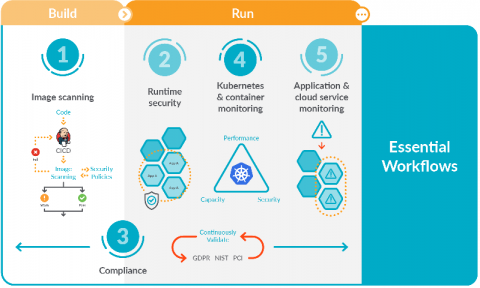
5 Essential workflows for secure DevOps
Focusing on these five essential workflows for secure DevOps will help you get started implementing monitoring, security, and compliance for containers and Kubernetes. You might be starting to adopt DevOps and find that it dramatically simplifies deploying applications in containers and Kubernetes. However, you probably also found that it adds a new set of complexities for managing, securing, and troubleshooting applications.
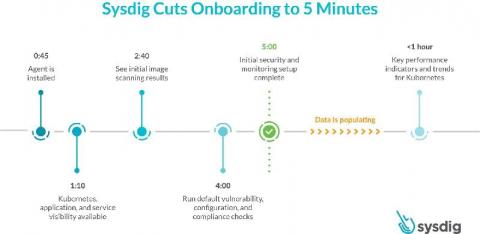
Sysdig cuts onboarding for container and Kubernetes visibility and security to 5 minutes
Today, we are excited to announce a faster onboarding for Kubernetes visibility and security. With the SaaS-first approach and new enhancements to the Sysdig Secure DevOps Platform, you can get results after just a five-minute setup. This release includes a new guided onboarding process, out-of-the-box dashboards as part of curated essential workflows, and a new Sysdig Essentials tier. 5 minutes to onboard secure DevOps - YouTube An error occurred.
Cyber Security: Understanding the 5 Phases of Intrusion
Here at Graylog, we have recently had an increase in conversations with security teams from leading companies. We want to share our key findings with the Graylog community. The good thing is that cybercriminals use a methodical approach when planning an attack. By understanding their process and knowing your network, you will be better prepared and able to stay one step ahead.
Using Non-Enterprise Gear in an Enterprise World
How to Incorporate Security Into Your company's SDLC
It’s been shown that if you follow a proven collection of practices for developing, designing, testing, implementing, and maintaining your software, you will produce a much higher quality product. Over the past few years, we have seen an increasing number of cases of attacks on the application layer. The Open Web Application Security Project, OWASP, estimates that around one-third of web applications contain security vulnerabilities.
Announcing the Tigera - Nutanix Partnership
Today we are pleased to announce our partnership with Nutanix, creators of the industry’s most popular hyper-converged infrastructure (HCI) technology. HCI combines datacenter hardware using locally-attached storage resources with intelligent software to create flexible building blocks that replace legacy infrastructure consisting of separate servers, storage networks, and storage arrays.
Kubernetes RBAC 101: Authentication
In part one of this series on Kubernetes RBAC, we introduced authentication and authorization methods. In this article, we’ll dive a little deeper into authentication — a prerequisite for RBAC. As we saw, there are a few authentication methods including client certificates, bearer tokens, HTTP basic auth, auth proxy, and impersonation. Because HTTP basic auth and statically configured bearer tokens are considered insecure, we won’t cover them here.
Why HTTPS is important for your website security
HTTP, which stands for Hypertext Transfer Protocol, is a communication protocol used by your browser to connect to the web server of the site you're looking for. When HTTP data transfer between the browser and the web server is shared via unencrypted hypertext, anybody connected to your network can intercept the data you're transferring. To combat this, it's best to switch to HTTPS, the more secure extension of HTTP. You can't verify data integrity with HTTP