Why it's important to use a VPN and how NoProx can help you stay private
Image Source: depositphotos.com
In today’s world, online security is of critical importance. There are solutions designed to protect your personal data and system from all sorts of threats. Choosing the right tools is important not only for individuals but also for entire companies. NoProx offers the most advanced and effective solutions for data protection, privacy, and maintaining anonymity.
Who collects your data online and how
Every time you go online, you leave a digital footprint. The information is collected and analyzed by a range of entities. And often, users aren’t even asked for consent, so we may not even realize that we’re sharing our data.
Data is collected:
- On social media
- When visiting websites
- In online stores
- When using various services
- By Internet providers
- When using apps (on both computers and smartphones)
- By cybercriminals (via phishing links, downloading malware, using public networks, etc.).
In general, data is collected for analytics, ad optimization, bot and attack protection, monitoring suspicious activity, for sale, etc.
How tracking works on websites
Web tracking allows websites and third parties to collect, store, and share information about user behavior. Websites track:
- IP. This helps determine a user’s location. That data is used for targeting and may also be used for blocking access. The IP can also reveal details about the OS, processor, screen resolution, and more.
- Cookies. These are small files stored in the browser after visiting a site. They allow the site to recognize you as a returning visitor.
- JavaScript. These scripts help collect data on clicks, link visits, time spent on the site, and other actions.
Internet tracking isn’t always bad. But it’s much safer to be informed, understand what’s being collected, and be able to decide which data you want to share.
The role of Internet providers in monitoring
Without encryption, your Internet provider can always see everything you do online. They have access to information about:
- Websites visited;
- Time and duration of your connection;
- Location and device identifiers;
- Data volume (sent/received).
In some cases, providers can see the specific pages you visit on a site and what you do there.
Data collection by ISPs happens for several reasons. First and foremost—security. It helps block unwanted sites, fight illegal content, enforce censorship laws, and, if needed, share logs with government agencies. Data tracking can also be used for commercial purposes by selling it to advertising platforms.
Examples of leaks and commercialization of personal data
Data leaks and the commercial use can be an unpleasant surprise. The issue has been confirmed by several high-profile cases:
- Google. In 2020, the company was fined multiple times in France, with total penalties reaching €50 million. The reason was that Google was installing cookies without user consent, a direct violation of the law.
- Facebook. This social network has repeatedly faced penalties. A notable example was when it conducted facial recognition on photos without informing users. Over 1.5 million users were affected, and each received nearly $350 in compensation following a court ruling. A more high-profile case occurred in 2019 when Facebook paid $5 billion for illegally sharing users’ private information with third parties.
- Equifax. The American credit bureau was hacked, resulting in the data of more than 145 million people being leaked. It became one of the largest cybercrimes in history.
What can a VPN do: real protection or illusion?
Not only sketchy websites but also major corporations can pose threats. Thus, VPN services are a popular solution. But users often ask a reasonable question—does this kind of data protection on the Internet work or is it just the illusion of safety?
IP address protection
VPN is the best answer to the question how to hide IP. It replaces the user’s address with the server’s address. As a result, you can:
- Bypass location-based blocks;
- Prevent tracking and data usage for targeting;
- Minimize the risk of DDoS attacks;
- Prevent the theft of personal information.
Traffic encryption
VPN uses encryption technology to prevent unwanted access to and viewing of your traffic. The protection process happens in stages:
- Connection to the server;
- Encryption of data;
- Data sent to the server from the site;
- Data delivered to your device and decrypted.
This creates an encrypted tunnel between the server and your device.
VPN as part of comprehensive cyber hygiene
VPN services can become a key part of a full cyber protection strategy. Using a VPN for security helps ensure:
- Anonymity online;
- Protection of private information;
- Secure access to files;
- Access to any content from anywhere in the world.
However, a VPN should be used in combination with other protection tools, such as antivirus software, which can prevent malware from being installed on your device and stop further tracking.
How to find your IP and why it is important to hide it from others
Users often ask how to find out their public IP address. The simplest and most accurate way is to visit a website that quickly shows this information. Use the what is my IP option for that. By the way, if you want to check your address through the network settings of your device (phone, laptop, or computer), it will most likely show only the local (private) address, while your public one is a different thing.
Keep in mind that it’s very important to hide your public IP address from malicious actors online because they can determine the approximate physical location of your computer by knowing your IP address. To do this, they simply run an IP lookup, and the system will return the country, region, city, provider name, and even show the physical location on a map. Sometimes that address may be someone’s personal address, but more often it’s the physical address of the Internet provider’s node that grants access to users. Anyway, here’s a list of reasons why it’s important to hide your public IP address (in addition to preventing physical tracking):
- Bypassing website content restrictions based on location
- Fighting intrusive online ads
- Increasing your online privacy.
What is the benefit of the NoProx service?
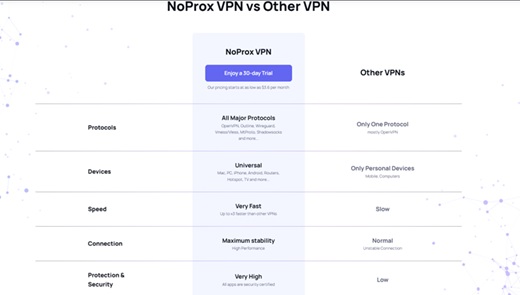
NoProx VPN offers comprehensive protection services for both individual and corporate users. We deliver optimal solutions, a high level of security, and user-friendly tools.
VPN protocols to choose from
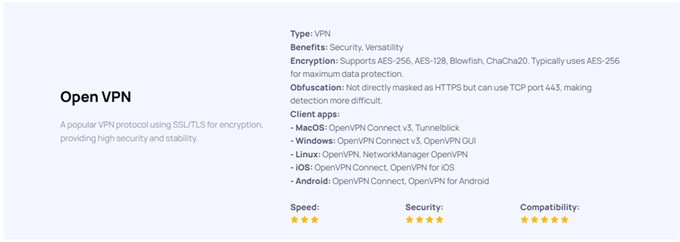
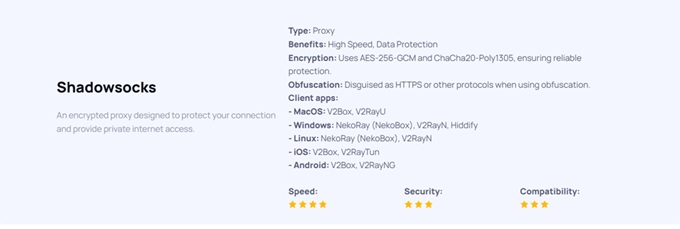
Choosing the right VPN protocol is key to cybersecurity. Available options include:
- WireGuard. A simple, modern, open-source option with strong encryption. It offers fast performance, stable connections, mobile device support, and minimal vulnerabilities. This is a great choice for constant use, as well as for gamers or streamers.

- OpenVPN. One of the most reliable protocols, offering flexibility, support for multiple encryption algorithms, and the ability to bypass firewalls. However, it requires more system resources and has more complex settings. This option is ideal for corporate environments.
- Shadowsocks. A lightweight protocol with high speed and easy setup. It does not provide full traffic encryption, so it’s best suited for basic protection and bypassing censorship.
Lack of logs
Using our own servers, we guarantee a high level of security and VPN privacy. We never store your logs or use your data for third-party sharing or sales. That means your activity with NoProx VPN remains completely anonymous.
Simple interface, quick start
Our solutions are designed for maximum ease of use. You can install the software in just a couple of clicks. Setup is quick and intuitive. Plus, our services support all modern devices and operating systems, including Windows, macOS, Android, iOS, and Linux.
NoProx is a modern security tool for ordinary users
If you’re looking for the most effective way to stay secure online, choose NoProx. Modern VPN services will provide safe surfing, protect your online activity from tracking and any outside threats.

