Operations | Monitoring | ITSM | DevOps | Cloud
What is Role-Based Access Control?
Most of us have visited a hotel at some point in our lives. We arrive at reception, if we request a room, they give us a key; if we are going to visit a guest, they lead us to the waiting room as a visitor; if we are going to have dinner at their restaurant, they label us as a customer; or if we attend a conference on technology, we go to their conference room.
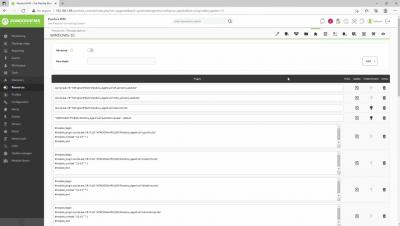
What's New Pandora FMS 759
Let’s take a look together at the features and improvements included in the new Pandora FMS release: Pandora FMS 759.
Update Manager |Pandora FMS|
Do you know what BYOD, BYOA, BYOT are? No? You lack experience!
We apologize in advance for this extremely freaky reference: If in the well-known science fiction saga Foundation there was a duty to collect all the information of the galaxy to save it, at Pandora FMS we have assigned ourselves the task of making a glossary worthy enough with all the “What are” and the “What is” of technology. And today, without further delay or freakiness, it’s time to define the acronyms: BYOD, BYOA, BYOT.
You are a sinner (of data management)!
Let’s get to the point about data management: Businesses need data, but accumulating too much can be detrimental. Data overcrowding can corrupt IT professionals, turning them into greedy hoarders. Being indigestible with excessive repeated, outdated or banal information, the so-called ROT data, is bad. Companies of the world! The Devil tempts you with Big Data! Something that, if too much, could be harmful! We tell you all about it in this article.
An unknown problem in the data center industry
The current global pandemic of Covid-19 has brought us a few gifts: global desolation, earaches from the rigid rubber bands of the FFP2 masks, applause for Health at eight in the afternoon on the balconies, fear of infected ones and staff shortage in the data center industry and shortage of IT professionals. In this article we will delve into this last topic.
Absolutely no one is safe from security attacks
Software developers and manufacturers around the world are under attack by cybercriminals. It is not like we are in a time of the year in which they spread more and they barricade themselves in front of the offices, with their evil laptops seeking to blow everything up, no. They are actually always there, trying to violate information security, and in this article we are going to give you a little advice on the subject.