Operations | Monitoring | ITSM | DevOps | Cloud
Are NoSQL Databases Relevant For Data Engineering?
SQL is great, but sometimes you may need something else. By and large, the prevalent type of data that data engineers deal with on a regular basis is relational. Tables in a data warehouse, transactional data in Online Transactional Processing (OLTP) databases — they can all be queried and accessed using SQL. But does it mean that NoSQL is irrelevant for data engineering?
10 Ways to Get Ahead with OpsRamp's AIOps
IT operations departments in larger enterprises often use 10-15 monitoring tools across different teams to track the health and availability of their core business services. Rather than helping ITOps teams gain a comprehensive view of their infrastructure, an overload of monitoring tools tends to only compound organizational silos and limit insights for incident troubleshooting. Yes, there is too much of a good thing.
Splunk for OT Security V2: SOAR and More
In the last 90 days, the news of cyberattacks on critical infrastructure has been stunning. From the unprecedented breach represented by Sunburst to the more recent bone-chilling attack at the Oldsmar water facility, the urgency to secure critical infrastructure in transportation, utilities, energy, water, critical manufacturing, telecommunications, healthcare, government facilities and the defense sector has never been higher.
Why Observability Is the Key Ingredient to Success
Digital transformation is accelerating at a staggering pace. Consider these statistics. In December 2019, Splunk partner Zoom had 10 million monthly active users. By the end of last year, that number was estimated to be closer to 300 million. It was part of an explosion of technological growth replicated across many industries and businesses in 2020. As Splunk CEO Doug Merritt said.
The Déjà Vu Evolution of Cloud Computing
I believe that the evolution to hybrid cloud is inevitable. Not because it’s grabbing headlines, but because it mirrors the industry’s history of new technology adoption. Take the evolution of virtualization, for example. Going back 20 years give or take, virtual machines popularized by VMware, KVM, and Hyper-V started to gain traction.
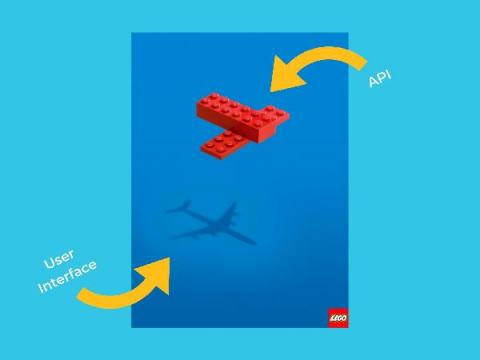
Why Your APIs Should Fly First Class
Picture yourself flying first class. You board the plane first, you get champagne, and you feel as though you’re the most important. Why not treat your APIs the same way? In this talk, FireHydrant CEO and Co-Founder, Robert Ross (a.k.a @bobbytables) shares why putting your APIs first can be a game-changer for your business and how this mindset shaped the way FireHydrant was built.
Efficiently Monitor the State of Redis Database Clusters
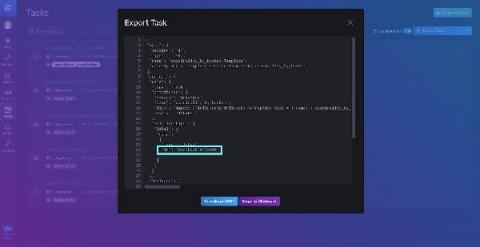
TL;DR InfluxDB Tech Tips: Debugging and Monitoring Tasks with InfluxDB
With InfluxDB you can use Tasks to process data on a schedule. You can also use tasks to write custom alerts. However, sometimes your task will fail. In this TLDR, we’ll learn how to debug your task with the InfluxDB UI and the InfluxDB CLI.
VPN and Firewall Log Management
The hybrid workforce is here to stay. With that in mind, you should start putting more robust cybersecurity controls in place to mitigate risk. Virtual private networks (VPNs) help secure data, but they are also challenging to bring into your log monitoring and management strategy. VPN and firewall log management gives real-time visibility into security risks. Many VPN and firewall log monitoring problems are similar to log management in general.