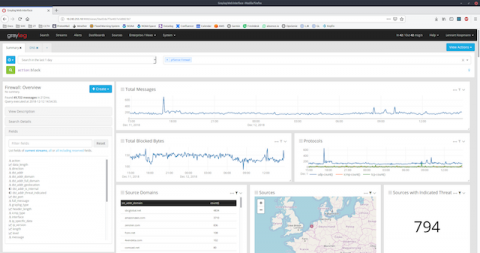
Getting Started with Graylog - Community Post
he Graylog community is what makes the product so exciting. It is awesome to see our community members take the time to help everyone over on our community forums, twitter, reddit or on their own private channels. I wanted to take some time to highlight a blog post by Community member BlueTeamNinja (aka Big Abe) who, after tackling a Graylog deployment shared lessons learned from a non-Linux/non-Elk person.