Operations | Monitoring | ITSM | DevOps | Cloud
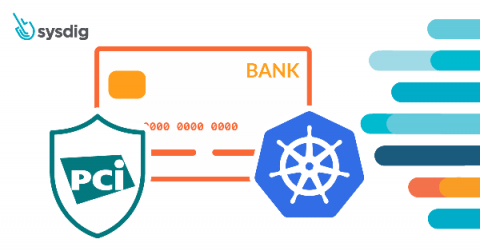
PCI Compliance for Containers and Kubernetes
In this blog, we will cover the various requirements you need to meet to achieve PCI compliance, as well as how Sysdig Secure can help you continuously validate PCI compliance for containers and Kubernetes. Learn how to meet PCI Compliance Requirements for Container and Kubernetes Environments!
Challenges using Prometheus at scale
This article will cover the most common challenges you might find when trying to use Prometheus at scale. Prometheus is one of the foundations of the cloud-native environment. It has become the de-facto standard for visibility in Kubernetes environments, creating a new category called Prometheus monitoring. The Prometheus journey is usually tied to the Kubernetes journey and the different development stages, from proof of concept to production.
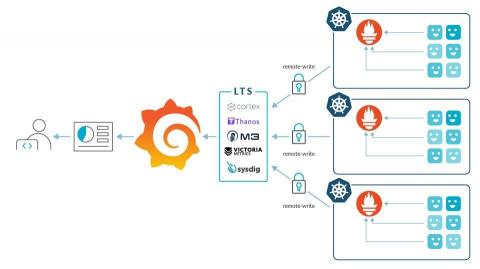
Sysdig Provides the First Cloud-Scale Prometheus Monitoring Offering
Sysdig Introduces the First Cloud-Scale Prometheus Monitoring Offering
Today, we are excited to announce a huge step forward for Sysdig Monitor. We’re introducing the ability for our customers to use Sysdig to scale Prometheus monitoring to millions of metrics with long-term retention. The improvements we are releasing make Sysdig the first cloud-scale monitoring offering to deliver full Prometheus compatibility.
PromCat: A resource catalog for enterprise-class Prometheus monitoring
PromCat, short for Prometheus Catalog, is a resource catalog for enterprise-class Prometheus monitoring. Prometheus has been revolutionary in the way we monitor our cloud-native environments, attracting immense attention from the open-source community and making the amount of Prometheus monitoring resources explode. Now, there are so many resources available that it’s no longer easy to filter out the good ones and discard those that are poorly documented or obsolete.
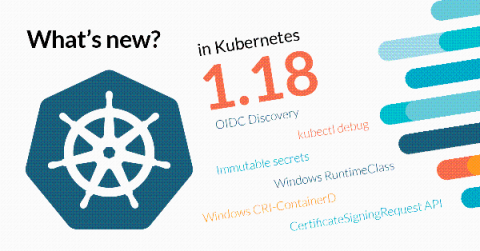
What's new in Kubernetes 1.18?
Kubernetes 1.18 is about to be released! After the small release that was 1.17, 1.18 comes strong and packed with novelties. Where do we begin? There are new features, like the OIDC discovery for the API server and the increased support for Windows nodes, that will have a big impact on the community. We are also happy to see how some features that have been on Alpha state for too long are now being reconsidered and prepared for the spotlight, like Ingress or the API Server Network Proxy.
Sysdig extends security control with VMware Tanzu Service Mesh
Sysdig is working with VMware to deliver enhanced microservice and cloud security. Leveraging the container runtime security capabilities of Sysdig Secure along with the operations and security policies of VMware Tanzu Service Mesh, built on VMware NSX, customers will be better able to accelerate Kubernetes and cloud adoption, as well as application modernization.
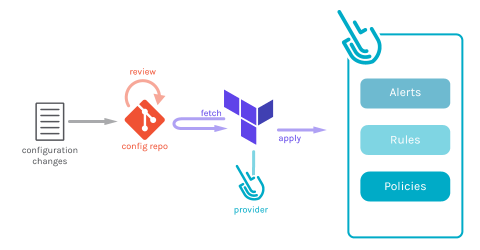
Announcing the enhanced Sysdig Terraform Provider
This article will show you how to leverage the Sysdig Terraform provider to follow Secure GitOps principles and use security as code in your infrastructure to define Alerts, Rules, and Policies.
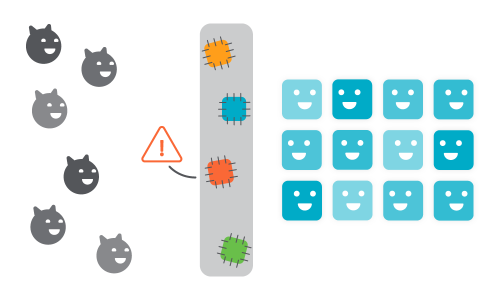
GitOps Security with k8s-security-configwatch
the k8s-security-configwatch GitHub Action, an open source tool from Sysdig, secures your GitOps workloads by detecting changes on your Kubernetes security configuration.