Operations | Monitoring | ITSM | DevOps | Cloud
Experimental feature: progressive releases
“No plan survives contact with the enemy.” This is a famous quote attributed to the Prussian field marshal Helmuth von Moltke. It is also quite applicable to software development: “No code survives contact with the user.” In mission-critical environments, staggered deployments of software are a crucial part of controlled updates, designed to ensure maximum stability of production applications and services.
Lockdown Bugfixes & Midnight Coding
It's been a strange few months here in Edinburgh. Thankfully Downtime Monkey has been largely unaffected by the lockdown, quietly continuing to monitor websites while the world shuts down. Coding from home has been challenging with kids off school and nurseries closed. However, in the twilight zone silent hours after everyone has gone to bed we've been developing improvements and fixing bugs. Here are the details...
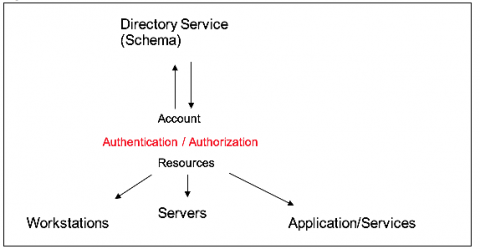
Monitoring Applications that use Okta for User Authentication
As the leading provider of identity and access management and authentication for enterprises, Okta gives employees, partners, suppliers, and customers secure access to the tools they need to do their most important work. With deep integrations to over 6,000 applications, the Okta Identity Cloud enables simple and secure access from any device.
A Blueprint for Running Stateful Services on Kubernetes
Managing stateful applications has been challenging for engineering and operations teams long before the debut of Kubernetes. In this post, we’ll explore all aspects of your deployments of stateful applications on Kubernetes, from the underlying hardware to Pod update strategies, and provide insights into how LogDNA uses stateful Kubernetes to build one of the world’s fastest log management platforms.
How to scale your monitoring with Sensu clustering
I recently led a webinar for the Sensu community on how to scale your monitoring by setting up a three-node cluster in Sensu Go using Sensu’s embedded etcd. Clustering improves Sensu’s availability, allows for node failure, and distributes network load. In this post, I’ll recap the webinar and provide demos on how to set up, back up, and restore your etcd cluster, including best practices for success.
Find What You Need! All About Our New Search Tool.
Product Releases Update Our new Search tool allows you to quickly build detailed queries without having to leave the page. Our new search tool expands on our column filtering feature. You can now create even more detailed queries by filtering on 20 unique criteria. New for this release is the ability to search Call Stack Function Names, Call Stack File Names, and Call Stack Line Numbers.
OpenStack Ussuri available on Ubuntu 18.04 LTS and 20.04 LTS
Quickly Duplicate Triggers Across Apps in AppSignal
We’re happy to announce that we’ve added a new feature which will make it easier for you to copy your trigger setup from one app to a new one. Anomaly detection triggers are a great way to get notified about unwanted events in your app. These anomalies are things like a high error rate, a lack of free disk space, or a high CPU usage. If your apps have a lot of the same requirements and infrastructure, you may have a lot of the same triggers across your apps.
How to deploy an app to AWS: Route 53 and DNS explained
In our series on how to deploy an app to AWS with the least effort, we've talked about getting started, preventive measures, and securing your app. Today, we're going to focus on DNS (domain name system), specifically the AWS DNS service Route 53. As you're deploying your web app, you will inevitably use DNS.