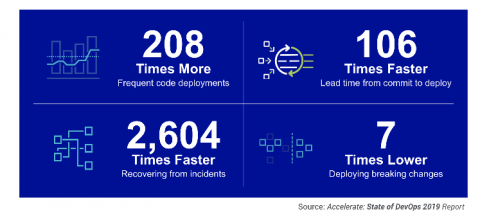
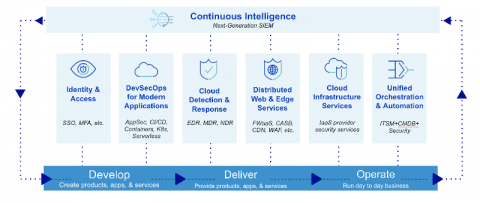
Insights from the 5th annual Continuous Intelligence Report
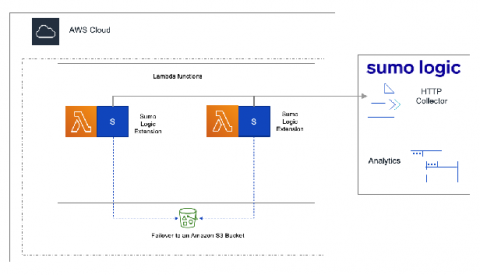
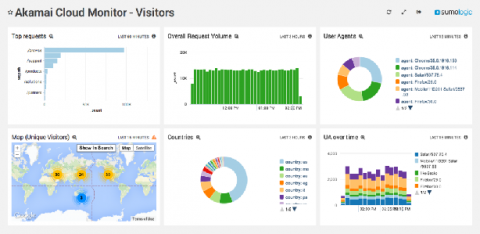
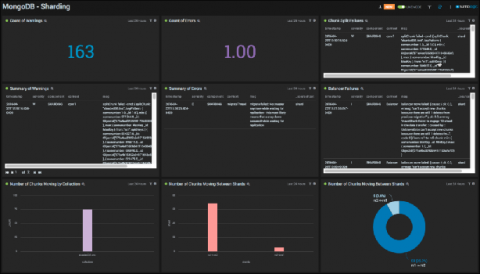
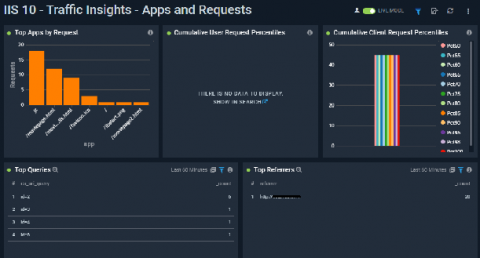
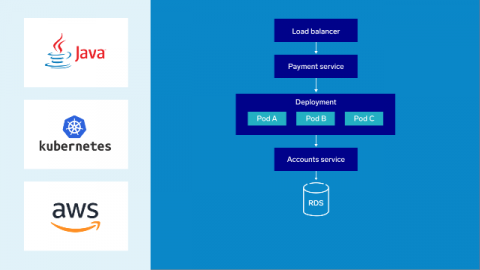
For five years, Sumo Logic has created the Continuous Intelligence Report on the state of modern apps and DevSecOps. New to this year’s report are unique insights into how enterprises are adapting to the COVID-19 pandemic— particularly in terms of security threats. Customers use Sumo Logic to manage their production apps and services, and this report provides a reflection of overall trends in technology adoption across entire industries.