Triaging Log Management Through SIEMS
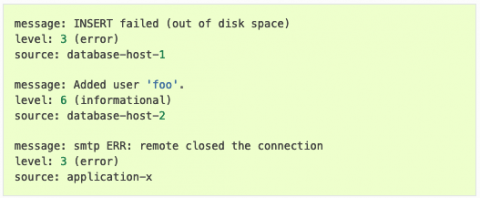
While all cybersecurity professionals agree that log management is integral for robust proactive and reactive security, managing the enormous amount of data logs can be a challenge. While you might be tempted to collect all logs generated from your systems, software, network devices, and users, this “fear of missing out” on an important notification ultimately leads to so much noise that your security analysts and threat hunters cannot find the most important information.