Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Cloud monitoring, security and related technologies.
Building complex Well Architected serverless architectures with Dashbird
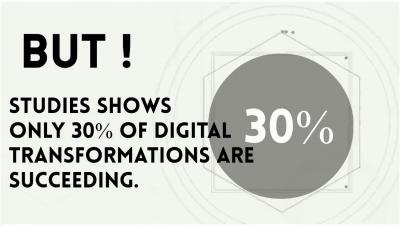
Looking for a Successful Digital Transformation Journey?
What is a single pane of glass?
There’s a new Azure agent in town – Azure Monitor Agent (AMA). I hear you saying, “Wait, aren’t there already enough Azure agents? So why another new agent?” A very valid question! Indeed, there are already a few Azure monitoring agents: the Log Analytics Agent, the Diagnostic Extension agent, and the Telegraf agent (and also the Dependency agent if you want to count it separately).
AWS Outage Ahead of Black Friday
Catchpoint detected an AWS outage earlier today, 25th November 2020. Enterprises that had their applications or services running on AWS US East 1 were impacted. Even some of the AWS products were impacted by the outage. We noticed Amazon services such as Athena slowing down at 5AM PST followed by intermittent HTTP 500 errors that started around 5:15AM PST. However, by 5:30AM PST, the fallout from the outage was evident.
AWS Well-Architected Framework in Serverless: Reliability Pillar
This is part three of the “Well-Architected in Serverless” series where we decipher the AWS Well-Architected Framework (WAF) pillars and translate them into real-life actions. In this article, we will focus on the AWS WAF Reliability (REL) pillar. Read Part 1 and Part 2. We have a Well Architected webinar coming up!
Cloud services
AWS Well-Architected Framework in Serverless: Operational Excellence
Welcome to part two of the five-part “Well-Architected Serverless” series. This article will discuss the second most crucial pillar of the AWS Well-Architected Framework (WAF): Operational Excellence (OPS). We have a Well Architected webinar coming up! To learn more about the AWS Well-Architected Framework (WAF) through the serverless lens and how to build Well-Architected architectures, make sure to attend our upcoming webinar on Friday, 27 November.
Introducing Inputs Data Manager on Splunk Cloud
Splunk Cloud’s ecosystem of apps and technical add-ons boasts a comprehensive set of input sources that enrich customer data insights. Many of these inputs reside in Cloud contexts, such as AWS, Salesforce, Azure, GCP, and many others. The Inputs Data Manager was introduced to aid the ingestion of these cloud data sources. As a result, in many cases, customers no longer need to host their own infrastructure to run scripted and modular inputs.
Zoom into Kinsing
The Kinsing attack has recently been reported by security researchers, and it is well known for targeting misconfigured cloud native environments. It is also known for its comprehensive attack patterns, as well as defense evasion schemes. A misconfigured host or cluster could be exploited to run any container desired by the attacker. That would cause outages on your service or be used to perform lateral movement to other services, compromising your data.