How to Use FastAPI [Detailed Python Guide]
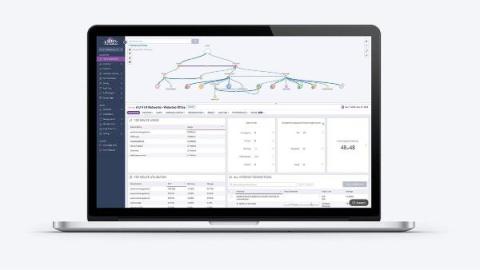
FastAPI Python combines modern Python features with high-performance web development capabilities. This framework stands out for its speed, ease of use, and built-in support for asynchronous programming. Whether you're building APIs, microservices, or full-stack applications, FastAPI offers tools to streamline your development process.