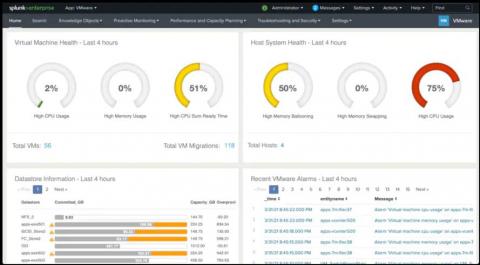
Detecting Password Spraying Attacks: Threat Research Release May 2021
The Splunk Threat Research team recently developed a new analytic story to help security operations center (SOC) analysts detect adversaries executing password spraying attacks against Active Directory environments. In this blog, we’ll walk you through this analytic story, demonstrate how we can simulate these attacks using PurpleSharp, collect and analyze the Windows event logs, and highlight a few detections from the May 2021 releases.