Operations | Monitoring | ITSM | DevOps | Cloud
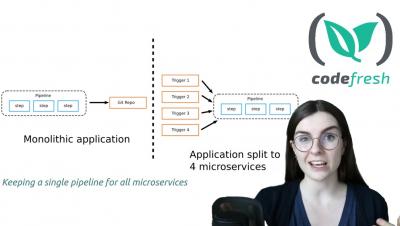
Reusable Pipelines for Microservices: Codefresh Quick Bites
Kubernetes Deployment Antipatterns - part 1
In our previous guide, we documented 10 Docker anti-patterns. This guide has been very popular as it can help you in your first steps with container images. Creating container images for your application, however, is only half the story. You still need a way to deploy these containers in production, and the de facto solution for doing this is by using Kubernetes clusters. We soon realized that we must also create a similar guide for Kubernetes deployments.
Kubernetes Deployment Antipatterns - part 2
This is the second part in our Kubernetes Anti-patterns series. See also part 1 for for the previous part and part 3 for the next part. You can also download all 3 parts in a PDF ebook.
Kubernetes Deployment Antipatterns - part 3
This is the third and last part in our Kubernetes Anti-patterns series. See also part 1 and part 2 for the previous anti-patterns. You can also download all 3 parts in a PDF ebook.
Combining Progressive Delivery With GitOps And Continuous Delivery
Code Coverage Reports using Codacy and Codefresh
Where do you usually track your code coverage? If you are not sure about the answer to this question or you would like to explore other options to the ones that you are currently using, then this post is for you. Specifically, this post details how you can use Codacy in your Codefresh pipeline to create and send coverage reports of your repository with every pipeline build. To follow along, make sure to have a Codacy and a Codefresh account. If not, now is the time to set-up a fresh account for free!
Combining Progressive Delivery with GitOps & Continuous Delivery
Codefresh vs Spinnaker
The appearance of containers and their performance benefits compared to the existing paradigm of virtual machines has forced several companies to rethink their software lifecycle, especially the delivery part. Continuous integration and deployment tools (CI/CD) are passing through a second renaissance phase which is characterized by new approaches centered around short-lived environments that are launched and destroyed in a much more dynamic way.
Why Kubernetes is a game-changer for E-commerce
When I started working at Purple managing the E-commerce stack, I inherited a single AWS EC2 instance that represented our entire infrastructure. The problem was, the company was doubling in size every few months, and with this exponential increase in load combined with the issues we were already experiencing with this infrastructure, it became a large business risk.