Operations | Monitoring | ITSM | DevOps | Cloud
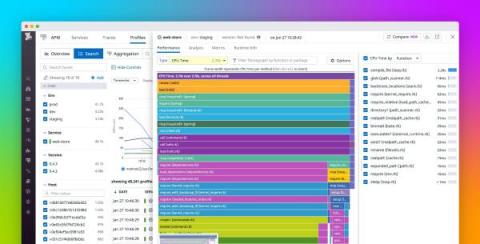
Analyze Ruby code performance with Datadog Continuous Profiler
Ruby is an object-oriented programming language celebrated for its simple and easy-to-read syntax. It powers Ruby on Rails, the open source web development framework that streamlines common development tasks involved in building web applications. We’re pleased to announce that our Continuous Profiler, which provides low-overhead, code-level performance insights, is now generally available for Ruby applications.
The PwnKit vulnerability: Overview, detection, and remediation
On January 25, 2022, Qualys announced the discovery of a local privilege escalation vulnerability that it identified as PwnKit. The PwnKit vulnerability affects PolicyKit’s pkexec, a SUID-root program installed by default on many Linux distributions. The same day of the announcement, a proof of concept (PoC) exploit was built and published by the security research community.
Elevate AWS threat detection with Stratus Red Team
A core challenge for threat detection engineering is reproducing common attacker behavior. Several open source and commercial projects exist for traditional endpoint and on-premise security, but there is a clear need for a cloud-native tool built with cloud providers and infrastructure in mind. To meet this growing demand, we’re happy to announce Stratus Red Team, an open source project created to emulate common attack techniques directly in your cloud environment.
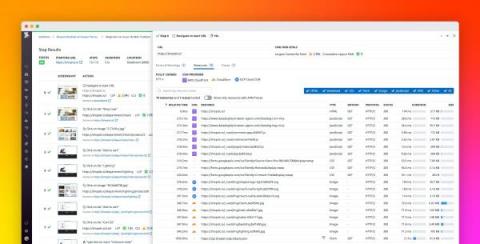
Monitor CDN performance within your Synthetic tests
Content delivery networks (CDNs) reduce latency by delivering cached data (e.g., JavaScript files, stylesheets, images, and videos) from a network of linked proxy servers to end users around the globe. CDNs help reduce the load on your origin servers and shorten the distance that data needs to travel, thus improving the end-user experience.
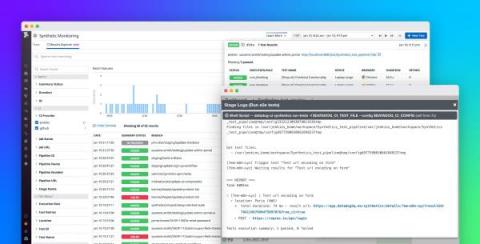
Run Datadog Synthetic tests in your Jenkins pipelines
Continuous integration (CI) has become the mainstream approach to software development as it enables organizations to iterate quickly while minimizing the risk of releasing faulty code. To implement CI, many organizations rely on Jenkins—one of the most mature and widely used automation servers on the market. Jenkins comes with hundreds of community-backed plugins to help you easily integrate it with other tools in your development workflow.
Datadog Network Performance Monitoring (NPM)
Datadog Cloud Security Platform
Best practices for building serverless applications that follow AWS's Well-Architected Framework
In part 1 of this series, we looked at common design principles and patterns for assembling microservices in serverless environments. But when it comes to building serverless applications, designing your architecture is only part of the challenge. You also have to ensure that each of your individual functions and services are secure, reliable, and highly performant—without incurring enormous costs.
Designing production-ready AWS serverless applications
Serverless has become an increasingly popular paradigm among organizations looking to modernize their applications as it allows them to increase agility while reducing their operational overhead and costs. But the highly distributed nature of serverless architectures requires developers to rethink their approach to application design and development. AWS-based serverless applications hinge on AWS Lambda functions, which are stateless and ephemeral by design.