Operations | Monitoring | ITSM | DevOps | Cloud
Powering Algorithmic Trading via Correlation Analysis
Finding relationships between disparate events and patterns can reveal a common thread, an underlying cause of occurrences that, on a surface level, may appear unrelated and unexplainable. The process of discovering the relationships among data metrics is known as correlation analysis. For data scientists and those tasked with monitoring data, correlation analysis is incredibly valuable when used for root cause analysis and reducing time to remediation.
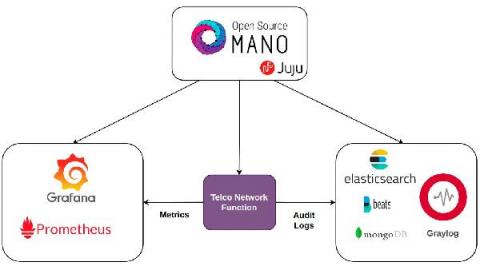
NFV orchestration: Network functions auditability with the open-source LMA stack
The transition to virtualized infrastructure and software network functions requires a re-evaluation in the telecom production environments. Network function is not alone. It has always been an important piece in the puzzle but requires a set of non-functional bits to complete the big picture and which brings the lifecycle management of network functions to the discussion.
Using HAProxy as an API Gateway, Part 6 [Security]
In almost every case, APIs have changed how modern applications connect to their data. Mobile apps, single-page web apps, IoT devices, integration hooks between software—all of these things rely on APIs to fetch, update, delete, and create data. In fact, one set of APIs might serve as the backbone of a website, mobile app, voice assistant device, and more, meaning one data store owns a treasure trove of information about us, the human users.
SOS - Don't Let a Microsoft Outage Drag You Down
You are at your desk, when all of a sudden there seems to be a hum that is growing louder, your heart starts to pound and you quickly realize that you might be in the midst of another Microsoft outage. You know that right now, Microsoft is your organization‘s core workforce engine and the backbone to ensure productivity - any outage or decrease in service quality can cause widespread productivity declines.