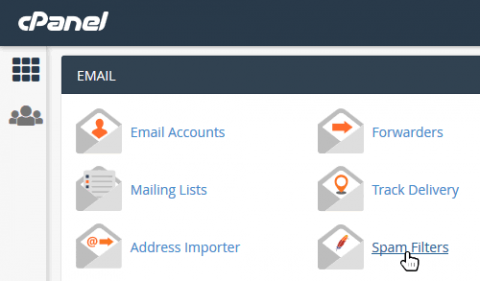
Whitelist Email Addresses in cPanel
In a recent blog post we answered the question: Why Whitelist an Email Address? TLDR; "If you expect to receive important emails from a trusted email address it is worth whitelisting the address to make sure that emails won't be accidentally blocked by an overzealous email client." In this post we show you how to do it in cPanel by adjusting the SpamAssassin spam filters. If you use cPanel webmail (e.g. Horde, Roundcube or Squirrel Mail) then this is what to do...