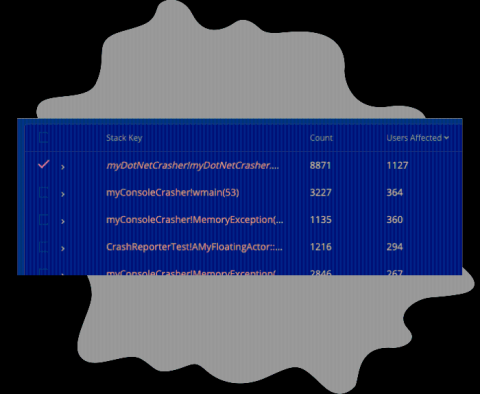
New Feature: Number of Users Affected by a Crash
We've just released a way to track the number of users affected by a crash! If you navigate to the Summary page, you'll now see a column labeled 'Users Affected’, this column shows how many unique users have been affected for each row in the crash summary table. With the data provided by this new column, you’ll have additional information available for prioritizing fixes. The ‘Count’ column is unchanged, and reports the total number of crashes reported by all users.