Introducing the new Sysdig Secure policy editor
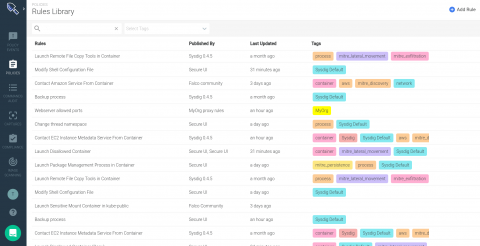
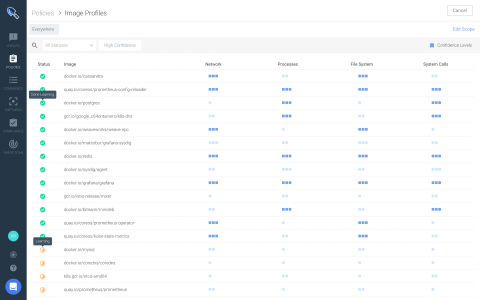
Among many other features Sysdig Secure version 2.4 introduces a new and improved runtime policy editor, along with a comprehensive library combining out-of-the-box run-time policies from our threat research teams, container-specific compliance standards, Kubernetes security and Falco opensource community rules.