Operations | Monitoring | ITSM | DevOps | Cloud
%term
Copying RDS Snapshots Between Regions
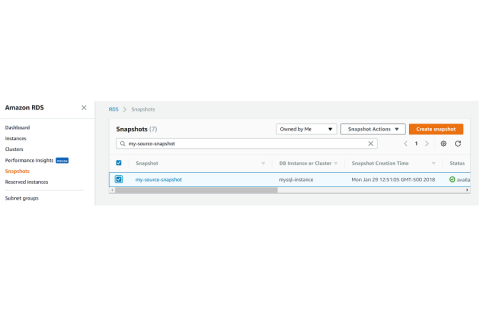
In our previous posts, I showed you how to copy your DB and Aurora snapshots to ensure they are preserved beyond the lifetime of your RDS instance. However, those copies were simply second copies in the same region as the original. In this post, I’ll show you how to copy your RDS snapshots to a second region for extra protection. Please note that I will restrict this post to unencrypted snapshots. Copying encrypted snapshots is more involved, so I’ll show that in a separate post.
Icinga Monthly Snap January: Releases, Events and #icingalove
January brought us many releases, new cool Icinga Web 2 themes and news about upcoming events.
8 Things to Monitor During a Software Deployment
Deployments don't have to suck! Identify any issues before they impact the end user. Learn 8 critical items you should monitor during your software deployments such as error rates, page load times, and apdex.
Monitive Mission Statement: "Why am I doing what I do?"
And no, it’s not summoning a few Venture Capital rounds of funding to pour them into a business, nor wasting my life on vacations or my money on gadgets. “What makes us happy?” I have to admit I’ve pursued this goal for a large part of my life. I know that some form of success is linked to happiness, and I know that success is not that esoteric feature that only the gifted among us get to possess. Success, just like happiness, is something we all have.
Top Nodejs Metrics To Watch
Encrypting an Unencrypted RDS Snapshot
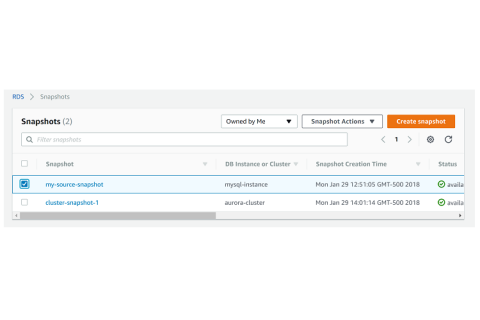
RDS snapshots can be unencrypted or they can be encrypted at rest. Today, best practice is to use encryption-at-rest on your RDS instances and clusters, and to encrypt your RDS snapshots. When you create an RDS snapshot from an RDS instance or cluster, the resulting snapshot will be encrypted if the source instance or cluster is encrypted. But if the source is not encrypted, then your RDS snapshot is not encrypted. When you create an RDS snapshot, you are not given the option to encrypt it.
TCP/UDP Monitoring
Let's talk about STIX, TAXII, and threat intelligence
In terms of collaboration, Structured Threat Information eXpression (STIX) and Trusted Automated eXchange of Indicator Information (TAXII) represent a revolution in the security industry. These protocols transformed the field of threat intelligence from a fragmented collection of information to a unified standard for information sharing. In this blog, I will examine this transition and how it came about.