Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on DevOps, CI/CD, Automation and related technologies.
Episode 10: Installing Redis from Ansible Galaxy
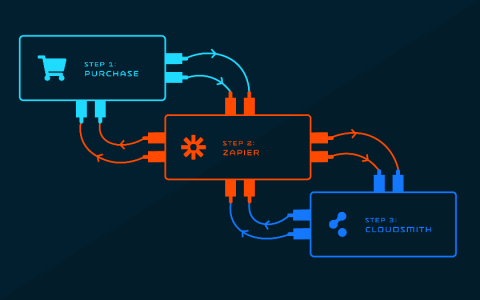
Vendors Connect. Powering digital distribution with Zapier & Cloudsmith.
At Cloudsmith, we are always looking for new ways to make our customers’ lives easier, more efficient and more highly automated. With this in mind we are extremely excited to announce that we have developed an official Cloudsmith Zapier integration!
Edge AI in a 5G world - part 2: Why make cell towers smart?
In part 1 we talked about the industrial applications and benefits that 5G and fast compute at the edge will bring to AI products. In this part we will go deeper into how you can benefit from this new opportunity.
Edge AI in a 5G world - part 3: Why 'smart cell towers' matter to AI
In part 1 we talked about the industrial applications and benefits that 5G and fast compute at the edge will bring to AI products. In part 2 we went deeper into how you can benefit from this new opportunity. In this part we will focus on the key technical barriers that 5G and Edge compute remove for AI applications.
The Anatomy of a Secure Serverless Platform, pt. I --- Design
A good software design tool enables rapid visualization of application architectures, much like a virtual whiteboard. A great design tool validates service architectures, their communication flows and the infrastructure required to execute them—and builds a scaffold that can be seamlessly taken forward into development. Security is a vital component of that scaffolding, starting at the design stage and extending through the application lifecycle.
Canonical announces Managed Apps to simplify enterprise cloud operations
The art of shipping and monitoring software with speed and confidence
FIPS 140-2: Stay compliant and secure with Canonical
FIPS 140-2 is a set of publicly announced cryptographic standards developed by the National Institute of Standards and Technology. It is an essential part of FEDRamp requirements for many governmental agencies in the US and Canada, as well as their business partners from all around the world. Furthermore, as a well established and verified security standard, an increasing number of large companies and financial institutions are asking for FIPS compliance.
IAM Access in Kubernetes: How to Install Kiam
In the last post, we compared kiam and kube2iam head-to-head. While kube2iam was declared the winner of that comparison, I feel that the case for kiam too compelling, and the setup too complicated, to not share my experience setting it up in production.