Operations | Monitoring | ITSM | DevOps | Cloud
3 Reasons Why Your Startup Should Move From Heroku To AWS
Heroku and AWS (Amazon Web Services) are the two most commonly used cloud services in present times. It lets a business deploy, monitor, and scale mobile and web applications. Both services are great for hosting applications and offer cloud computing resources. Choosing the best hosting service becomes difficult when you take a glance at the plethora of products that AWS offers. In case you are planning to switch to AWS from Heroku, you have come to the right place.
Event Log Management and Monitoring
Computer networks all around the world generate daily records of events occurring in their system. Some events are routine while others indicate potential security breaches or weak network health. Event log files consist of log information that can help organizations reduce their exposure against malware, intruders, damages and legal obligations.
How to SRE without an SRE on your team
Editor X - a Responsive Builder for Your Next Website
Welcome to 2020: the year in which having a business simply can’t happen without having a website. And, in recent years, not just ANY website. Business owners must have THE website: an online virtual space that is so magnificently created and intuitive to use, not to mention flame up emotions we never knew existed that users simply can’t forget. But how do you achieve this in a world with SO MANY WEBSITES without having to spend weeks if not MONTHS creating it?
Causal Inference: Determining Influence in Messy Data
When analysing data one of the biggest questions you may often face is: what is causing this situation? In this blog, we’re going to look at how causal inference can be used to understand in more detail what the biggest influencing factors are across a dataset. Traditionally in Splunk, we talk about correlation; does metric x go up or down in accordance with metric y or is there a relationship between x and y?
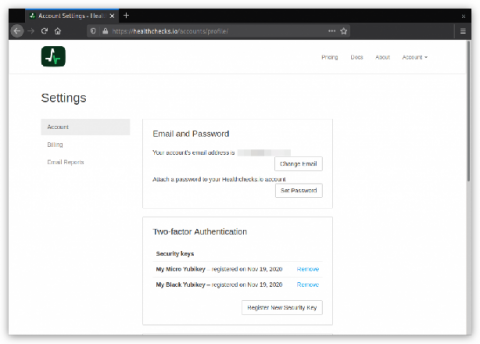
Two-factor Authentication
Healthchecks.io now supports two-factor authentication using the WebAuthn standard. Here is how it works: in the Account Settings page, users can see their registered FIDO2 security keys and register new ones.
Embedded Linux for teams
A Linux kernel for each developer team, which uses it to bring up target boards. Bespoke, built, issued, and maintained over years by the vendor. Teams that focus on building great apps, rather than figuring out hardware dependencies. Happy developers that bootstrap smart devices in no time. This is what highly productive embedded systems development should look like. Let’s unpack that vision.
5 Remote Working Best Practices and Tips in the Era of Coronavirus Pandemics
As the COVID-19 pandemic sweeps the world, the need has arisen for workers everywhere to adopt remote working practices wherever possible. Remote working presents many opportunities for both businesses and individuals to make better use of their time and enjoy a more streamlined approach to task delegation. Through the use of specialized software, such goals can be achieved without demanding more of individual team members or managers.
Solve storage monitoring woes with OpManager
Data in your enterprise organization doubles almost every year, and data multiplication at this pace requires boosting your storage capacity. But when the magnitude of data size increases, latency or performance lags are inevitable. You can outsource your storage infrastructure management to a third-party, but this might place your data at risk from security threats. The correct approach is to install a dedicated storage monitoring solution in your network. Fair enough! But is it essential?