Operations | Monitoring | ITSM | DevOps | Cloud
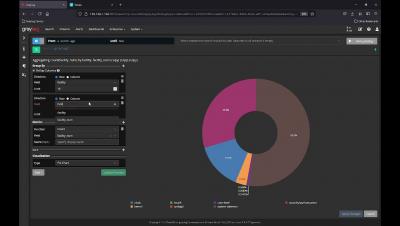
HTTP JSON Web API Input - COVID Dashboard
Bolster OT Security with Graylog
Anyone tracking the evolution of the IT industry is probably familiar with the concept of Industry 4.0. Essentially, it describes the process by which traditional industrial tasks become both digitized and continually managed in an IT-like fashion via modern technologies like cloud computing, digital twins, Internet of Things (IoT) sensorization, and artificial intelligence/machine learning.
Docker Compose on Raspberry Pi4
What's New In 4.1
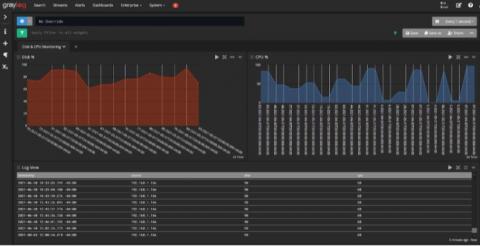
Graylog Logview
Supercharge Storage Optimization Via Graylog
Just how smart is your storage management? Storage is one of the most promising ways to shift from the "more is better" philosophy to the "work smarter" philosophy. What do I mean by that? Historically, IT managers who needed more storage responded in the most obvious way: they bought more. Then they deployed it, integrated it, and waited until the problem recurred.
Drive Successful AI Projects with Graylog
Many IT professionals think of Graylog primarily as a security (SIEM) solution, and of course it can be used in that way to great effect. However, Graylog’s industry-leading log aggregation, search, visualization, and classification capabilities go far beyond that role alone.
How to Upgrade Graylog In Docker
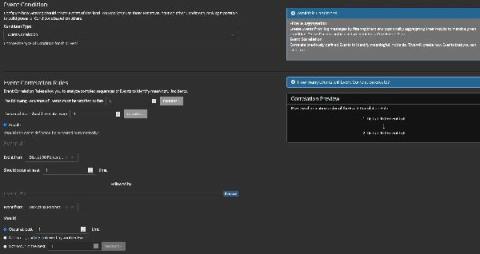
Graylog Illuminate: Getting Started with Sysmon
The Windows System Monitor (Sysmon) is one of the chattiest tools. With all the information coming in, it can be difficult and expensive to use it efficiently. However, the Graylog Illuminate package gives you a way to fine-tune it so that you can get better data and manage your ingestion rate better. Sysmon gives you awareness of what’s going on in your endpoints.