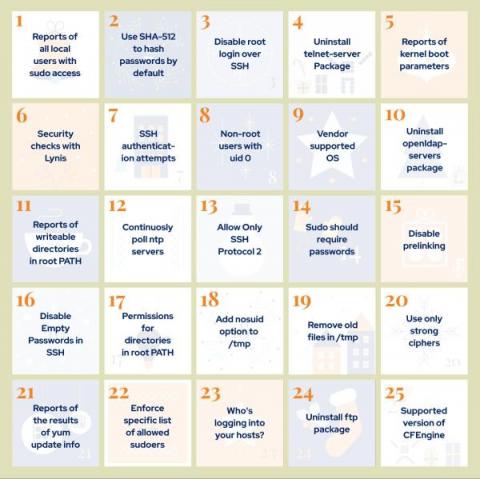
Security hardening holiday calendar - Week 4
This is the final summary of our 2021 security hardening holiday calendar. We wanted to provide educational, useful, and actionable security advice, and we’re really pleased with the reception! Thank you for reading and following along.