Operations | Monitoring | ITSM | DevOps | Cloud
Latest News
JFrog's Bold Roadmap: The Rise of Binaries
Lambda Execution Leaks: A Practical Guide
At Lumigo, we recently ran into some issues with a service we built on top of our Nodejs AWS Lambda handler. These issues were the result of lambda execution leaks from within our serverless code. In this article, I’ll explain about node.js lambda execution leaks and how to avoid them.
Improve Customer Experiences & Collaboration Between Support and Engineering With Bidirectional Communication
We are delighted to announce our new PagerDuty integration for Salesforce Cloud. This integration empowers Customer Service, Engineering, and IT teams to proactively resolve customer issues in real time by improving communication and collaboration.
Eliminate the Fog: The Path to Microsoft 365 Monitoring Visibility
I’ll go out on a limb and venture a guess that everybody reading this blog has had challenges adjusting to life in a post COVID world. I certainly have. My latest challenge? Navigating the simultaneous use of a face mask in public venues while wearing glasses to read stuff that’s more than 20 feet away. Just like ski and water goggles, my prescription specs also fog up when simply taking a leisurely stroll through the grocery store.
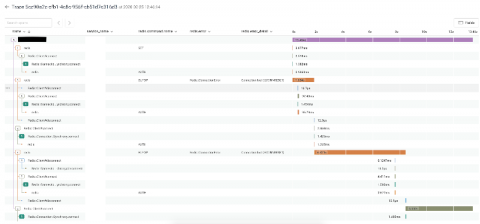
Using Honeycomb to Investigate a Redis Connection Leak
This is the story of how I used Honeycomb to troubleshoot redis/redis-rb#924 and discovered a surprising workaround.
Kubernetes observability tutorial: Metrics collection and analysis
This post is the second in our Kubernetes observability tutorial series, where we explore how you can monitor all aspects of your applications running in Kubernetes, including: We’ll cover using Elastic Observability to ingest and analyze container metrics in Kibana using the Metrics app and out-of-the-box dashboards.
Elasticsearch sniffing best practices: What, when, why, how
Elasticsearch powers search experiences for so many tools and apps used today, from operational analytics dashboards to maps showing the closest restaurants with patios so you can get out of the house. And in all of those implementations, the connection between application and cluster is made via an Elasticsearch client. Optimizing the connection between the client and the Elasticsearch cluster is extremely important for the end user’s experience.
Personal Information Security and OnPage's Commitment to User Privacy
When making purchasing decisions, organizations must consider a vendor’s product pricing, promised benefits and level of customer service. Thorough vendor evaluation tends to result in successful investments, allowing organizations to reap the benefits of their newly acquired products without buyer’s remorse. Unfortunately, some buyers dismiss the importance of personal information security and how the vendor promises to protect user data.
Complete Guide to Lambda Triggers and Design Patterns (Part 1)
A while ago, we covered the invocation (trigger) methods supported by Lambda and the integrations available with the AWS catalog. Now we’re launching a series of articles to correlate these integration possibilities with common serverless architectural patterns (covered by this literature review). In Part I, we will cover the Orchestration & Aggregation category. Subscribe to our newsletter and stay tuned for the next parts of the series.