Operations | Monitoring | ITSM | DevOps | Cloud
Security
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Kroger Uses JFrog Xray for Software Security and License Compliance
AppDynamics' response to our customers regarding the Log4j vulnerability threat
We know that the threat posed by the Log4j vulnerabilities is top of mind — and we’re here to help. Bookmark this post for ongoing updates.
Security vulnerabilities on the Data Distribution Service (DDS)
If you are currently running the Robot Operating System 2 (ROS 2), this piece is especially relevant to the security of your robots. A few weeks ago, a group of security researchers reported 13 security vulnerabilities affecting some of the most used implementations of DDS, the default middleware used by ROS 2.
The Log4j Log4Shell vulnerability: Overview, detection, and remediation
On December 9, 2021, a critical vulnerability in the popular Log4j Java logging library was disclosed and nicknamed Log4Shell. The vulnerability is tracked as CVE-2021-44228 and is a remote code execution vulnerability that can give an attacker full control of any impacted system. In this blog post, we will: We will also look at how to leverage Datadog to protect your infrastructure and applications.
Log4j gets added to the code "wall of shame."
It seems that every few weeks, we are alerted to a new significant security issue within one of the plethoras of code elements that are widely used. The same pundits discuss the same range of concerns with open-sourced code each time. The list of “usual suspects” is long, and I know I could add at least 20 additional “reasons” to this list without thinking about it too hard. I’m not sure that open-sourced code is riskier than proprietary developed code. There I said it.
Security hardening holiday calendar - Week 2
This december, we are posting security advice and modules, every day until December 25th. Now, it’s December 14th, and we’ve gotten to the fourteenth day of the security hardening holiday calendar.
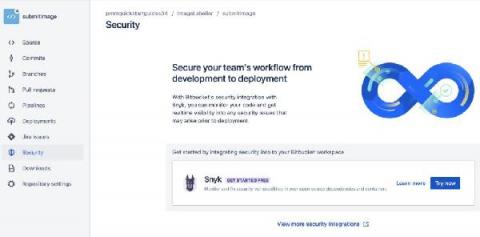
Log4shell fix with the Bitbucket Cloud and Snyk integration
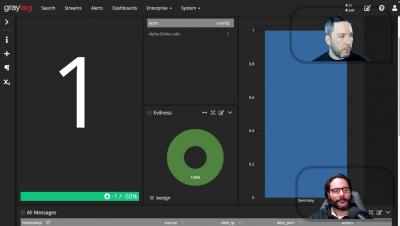
Managing Your SIEM EPS License with Cribl LogStream
We see unfriendly customer practices all around in the SIEM space. For example, some major SIEM vendors use an Events Per Second (EPS) license model to monetize access to their tools. Typically, these vendors will drop data above the EPS license or stop data ingestion to incentive license compliance if you run over your EPS license. These license controls disrupt operations and risk enterprise security posture, which can cause chaos.
The Principles of DevSecOps
As a Solution Architect here at xMatters, an Everbridge Company, and through my 30-year career in the IT industry, I've seen many frameworks offering bold new ideas. CMMI, ITIL, Prince 2, Agile, Scrum, and most recently, DevOps. These frameworks come and go, offering huge improvements in the way we deliver and manage our IT capabilities, but never lasting long enough to act on those promises. That's not to say they haven't made a marked difference in the IT space, or that they haven't been hugely impactful for organizations around the globe. They become launching off points for a new framework, and now there's a new term that's appeared, DevSecOps.