Operations | Monitoring | ITSM | DevOps | Cloud
Security
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
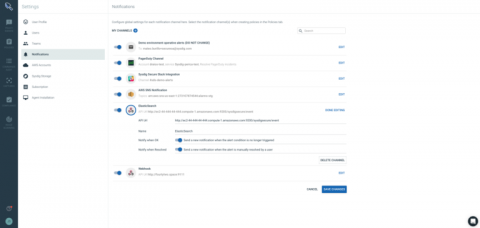
Using Terraform for container security as code with Sysdig Secure
In the following tutorial you can learn how to implement container security as code. You probably have a CI/CD pipeline to automatically rebuild your container images. What if you could define your container security as code, push it into a Git repository to version control changes and then enforce your policy in your container orchestration tool like Docker or Kubernetes using Sysdig Secure?
All the Security and Compliance Features Announced at AWS Re:Invent 2018
Yet another Re:Invent has concluded, leaving behind a trail of announcements, new features, and vendor swag (how many T-shirts can we possibly own?). Security was a hot topic at this year’s conference; so much so that it was mentioned in-depth within the first 10 minutes of Andy Jassy’s keynote and numerous times afterwards, as well as during Werner Vogel’s keynote the following day.
Policy-driven Secure Application Connectivity for OpenShift
What GDPR Means for Log Management
CFEngine 3.12.1 LTS Released
CFEngine 3.12.1 LTS has now been released. This release brings many stability and performance improvements to the 3.12 LTS series. It is a stable and well-tested version of CFEngine. We wish to extend a big thanks to the ecosystem that helps make CFEngine great by reporting bugs, contributing fixes and suggesting new and improved functionality. Without you, CFEngine would not be the powerful, high performance, widely used product we all appreciate today!
SaaS Security: Securing Zenoss in a SaaS World
The Gospel of DevSecOps: Partnering to Love Thy Customer
Raise your hand if you’re a believer in DevOps—thank you, I see that hand. As a former organizer of devopsdays Toronto (2014 – 2016), you could say that I drank the Kool-Aid early on. But thanks to the outstanding research of the DevOps Research Association (DORA) and numerous State of DevOps reports before it, DevOps culture is much less of a religious battle than it has been in the past.
One Planet York: Data Breach Update
RapidSpike would like to make a statement about how one of our developers assisted the City of York Council with a potential data breach on their One Planet York mobile app in early November.
Conquer it with correlation-Part 1: The advanced persistent threat (APT)
Among all the pesky attacks that keep security administrators working late, advanced persistent threats (APTs) are possibly the most lethal. An APT is a long-term, targeted attack which involves stealthily spying on an organization’s network activity or siphoning off sensitive data, as opposed to openly damaging or locking down network resources.