Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Containers, Kubernetes, Docker and related technologies.
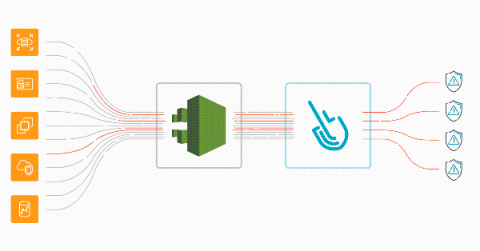
Automate Fargate image scanning
Discover how to automate AWS Fargate image scanning directly in your AWS environment and block vulnerabilities from reaching production, among other threats. AWS Fargate and ECS allow you to deploy containerized workloads quickly. Fargate is even more convenient, as you don’t have to take care of the infrastructure.
AWS threat detection using CloudTrail and Sysdig Secure
Implementing AWS threat detection with Sysdig Secure takes just a few minutes. Discover how to improve the security of your cloud infrastructure using AWS CloudTrail and Sysdig Cloud Connector. With the rise of microservices and DevOps practices, a new level of dangerous actors threatens the cloud environment that governs all of your infrastructure. A malicious or inattentive cloud API request could have a sizable impact on availability, performance, and last but not least, billing.
Set up Let's Encrypt TLS Encryption using the HAProxy Kubernetes Ingress Controller
Securing and Monitoring AWS Container Services
Puppet Camp America Central: Puppet Infrastructure in Kubernetes
What is an inode and what are they used for?
Inodes, speculated to be short for “index nodes,” have been around since the introduction of the first UNIX file system around the late 1970s. They were adopted into Linux in the 90s—and for good reason. They’re an excellent way to keep track of how your files are stored, and the method many systems are still based on today.