Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on DevOps, CI/CD, Automation and related technologies.
How to make your software team awesome: Get the inside scoop with DORA
It's out of the Oven: Bun 1.0 support is here
Using Tailscale for Authentication of Internal Tools
JWT is a popular way for authentication and authorization, especially for service to service communications. When it comes to internal tools, distribution and renewal of JWT can become a challenge. Our internal support systems use JWT to authenticate and authorize access and they are written in a few different languages and run on different hosting options.
Building an E2E Ephemeral Testing Environments Pipeline with GitHub Actions and Qovery
How telcos are building carrier-grade infrastructure using open source
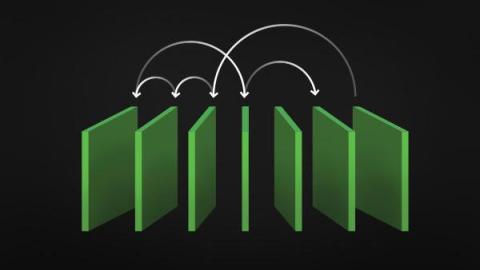
Argo Rollouts at CircleCI: Progressive deployment for agile and efficient releases
At Circle, our traditional approach to Kubernetes (k8s) deployments likely looks familiar to many of you: Run the workflow, create the image, build the Helm chart and deliver it to k8s. At that point, k8s takes over with its rolling update. This method gets the job done, but we knew it wasn’t ideal. Limited support for canary releases and the need for time-consuming error monitoring and manual rollbacks added friction and risk to our release processes.
DevOps Speakeasy with Bruce Schneier
Practical guidance for getting started as a site reliability engineer
At the beginning of May, I joined incident.io as the first site reliability engineer (SRE), a very exciting but slightly daunting move. With only some high-level knowledge of what the company and its systems looked like prior to this point, it’s fair to say that I didn’t have much certainty in what exactly I’d be working on or how I’d deliver it.