Operations | Monitoring | ITSM | DevOps | Cloud
End to End Tracking for Azure Integration Solutions
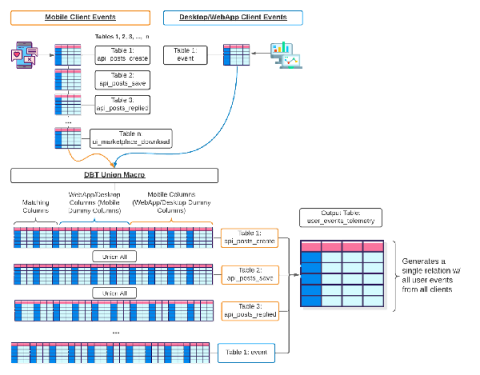
Manage Dynamic Schemas at Scale with Rudderstack & dbt
I recently had the pleasure of hosting a webinar with the team over at Rudderstack. It focused on Data Engineering and managing dynamic schemas at scale. More specifically, Rudderstack-generated, dynamic schemas at scale. This blog will discuss the tools, software, and methods to do just that.
AIOps: Clearing the Path for Automated Operations
In the ScienceLogic webinar, “Clearing the Path for Automated Operations,” we look at how one global technology organization got their IT house in order through the application of AIOps and a strategic approach to implementation, based on ScienceLogic’s AIOps Maturity. ITOps teams are overloaded with manual, repetitive work that creates management bottlenecks and takes time away from new projects.
Kubernetes security issues: An examination of major attacks
In a never-ending game of cat and mouse, threat actors are exploiting, controlling and maintaining persistent access in compromised cloud infrastructure. While cloud practitioners are armed with best-in-class knowledge, support, and security practices, it is statistically impossible to have a common security posture for all cloud instances worldwide. Attackers know this, and use it to their advantage. By applying evolved tactics, techniques and procedures (TTPs), attackers are exploiting edge cases.
Generating DDL Statements to Recreate Single Objects
Extend Your APM Capabilities With End-User Data
A Policy Change To Prevent Abuse on JFrog Cloud
What's the ROI? How Operational Maturity Improves Customer and Team Satisfaction
Are we looking at the new normal now? In the last 18 months, organizations all over the world were compelled to undergo a rapid digital transformation and mature their operations to support services that were under unprecedented strain. Digital transformation allows companies to embark on large-scale cloud migrations and adopt modern development methods like DevOps and Agile.
My honest review: I tried AWS Serverless Monitoring using Dashbird.io
As a startup, we always want to focus on the most important thing — to deliver value to our customers. For that reason, we are a huge fan of the serverless options provided by AWS (Lambda) and GCP (Cloud Function) as these allow us to maintain and quickly deploy bite-size business logic to production, without having to worry too much about maintaining the underlying servers and computing resources.