Operations | Monitoring | ITSM | DevOps | Cloud
TL;DR InfluxDB Tech Tips - Using and Understanding the InfluxDB Cloud Usage Template
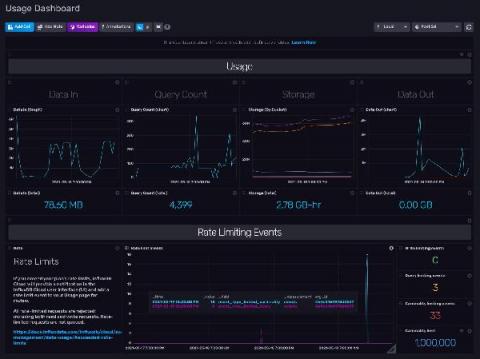
So you’re using InfluxDB Cloud, and you’re writing millions of metrics to your account. Whether you’re building an IoT application on top of InfluxDB or monitoring your production environment with InfluxDB, your time series operations are finally running smoothly. You want to keep it that way. You might be a Free Plan Cloud user or a Usage-Based Plan user, but either way, you need visibility into your instance size to manage resources and costs.
Using data to accelerate time to business value
Last year, European organizations spent $300 billion on digital transformation, according to IDC. Yet, only one in four businesses is realizing an appropriate return on investment (ROI) from it.
Why companies need URL filtering for enhanced cloud protection
The cloud landscape is rife with unsafe URLs and inappropriate content. This—coupled with the accelerated adoption of cloud applications in the workplace—has created an urgent need to scrutinize and control the use of these online resources to prevent data theft, exposure, and loss. This blog elaborates on how a robust URL filtering solution can help manage what cloud services your employees use and how they interact with these services.
5 Tips for SaMD Development
Secure Software Development: How to Check Your Code
Five worthy reads: Internet of Behaviors - Exploring beyond the Internet of Things
Five worthy reads is a regular column on five noteworthy items we’ve discovered while researching trending and timeless topics. This week let’s welcome a new acronym to the club — IoB (Internet of Behaviors) and assess its impact. Organizations are making the best use of analytics, A/B testing, and more amazing things to map the perfect customer journey. Here comes the missing piece to building an ideal user journey: Internet of Behavior (IoB).
How to Hire an Operations Manager
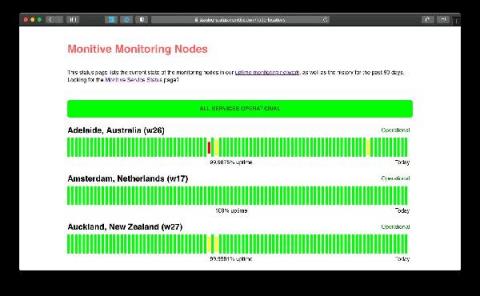
Status Pages Now Available
Unlimited Status Pages now available for all Monitive Pro users. Build trust, showcase reliability and inform your users of downtime in a professional way.