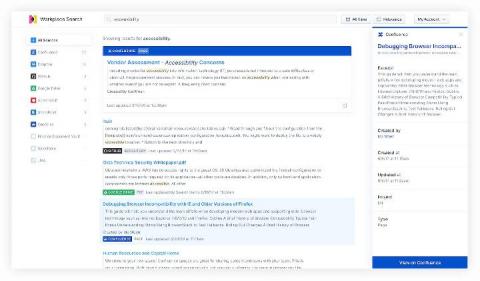
Searching Salesforce: Boosting your teams' productivity with Elastic Workplace Search
“If it’s not in Salesforce, it didn’t happen.” You’ve undoubtedly heard it, or perhaps you’ve said it yourself. And why not? Over the past 15 years, Salesforce has redefined the CRM industry, becoming the de facto solution for managing sales, customer service, marketing automation, and analytics functions with its cloud-only approach. As Salesforce’s solutions have expanded so has their user base.