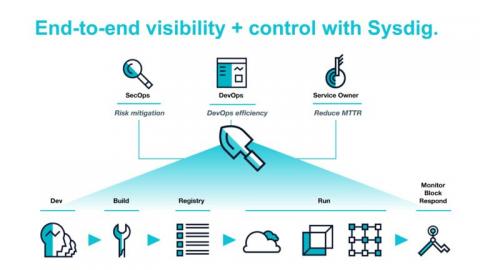
Announcing the Sysdig Cloud-Native Visibility + Security Platform 2.0
Today we’re announcing version 2.0 of the Sysdig Cloud-Native Visibility + Security platform. It provides a more powerful and significantly simpler way for enterprises to see the health, risk, and performance of their cloud-native environments in a single unified view.