Operations | Monitoring | ITSM | DevOps | Cloud
I Wish Someone Had Squished That Phish
Security Spotlight: Ryan Kovar
Splunking AWS ECS Part 2: Sending ECS Logs To Splunk
Welcome to part 2 of our blog series, where we go through how to forward container logs from Amazon ECS and Fargate to Splunk. In part 1, "Splunking AWS ECS Part 1: Setting Up AWS And Splunk," we focused on understanding what ECS and Fargate are, along with how to get AWS and Splunk ready for log routing to Splunk’s Data-to-Everything platform.
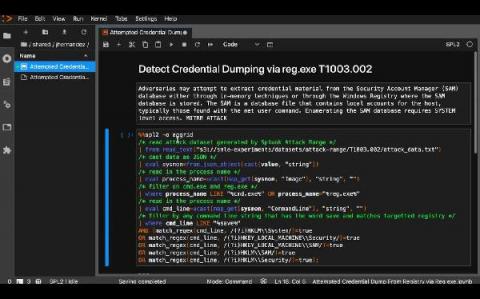
A Path to Proactive Security Through Automation
The sheer number of cyberattacks launched against organizations every year is massive and growing. If you’re a security analyst working in a SOC or security team, tasked with defending your organization, that means you’re getting bombarded by many more attacks than the recorded numbers above would suggest. These attacks translate into security alerts — fired from your various security tools — that you must investigate and resolve.
Introducing Splunk OpenTelemetry Java Lambda Wrapper
AWS Lambda has become a core technology in the shift to cloud-native application development, eliminating infrastructure management and fixed costs. But there are trade-offs with serverless environments. Not having access to the production infrastructure can make debugging difficult and there are a lot of moving parts, adding distributed complexity. Monitoring serverless functions in production requires observability beyond CloudWatch logs and metrics.
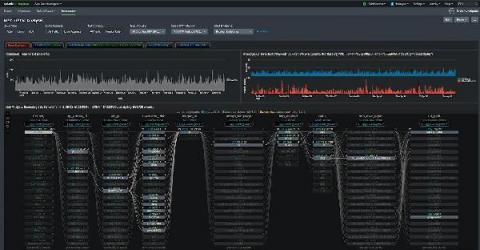
Advanced Link Analysis: Part 1 - Solving the Challenge of Information Density
Link Analysis is a data analysis approach used to discover relationships and connections between data elements and entities. This is a very visual and interactive technique that can be done in the Splunk platform – and is almost always driven by a person, an analyst or investigator, to understand the data and discover necessary insights specific to the business problem at hand.
Threat Hunting With ML: Another Reason to SMLE
Security is an essential part of any modern IT foundation, whether in smaller shops or at enterprise-scale. It used to be sufficient to implement rules-based software to defend against malicious actors, but those malicious actors are not standing still. Just as every aspect of IT has become more sophisticated, attackers have continued to innovate as well. Building more and more rules-based software to detect security events means you are always one step behind in an unsustainable fight.
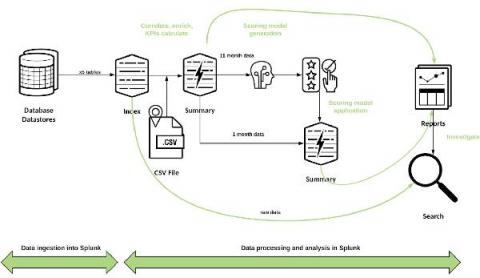
Creating a Fraud Risk Scoring Model Leveraging Data Pipelines and Machine Learning with Splunk
According to the Association of Certified Fraud Examiners, the money lost by businesses to fraudsters amounts to over $3.5 trillion each year. The ACFE's 2016 Report to the Nations on Occupational Fraud and Abuse states that proactive data monitoring and analysis is among the most effective anti-fraud controls.
The OpenTelemetry Tracing Specification Reaches 1.0.0!
OpenTelemetry hit an exciting milestone this week. The tracing specification has achieved v1.0.0, and the general availability of tracing APIs and SDKs is imminent!