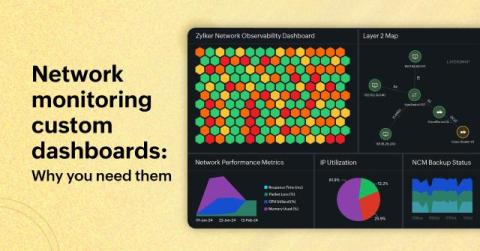
Creating custom dashboards for network monitoring with Site24x7
Instead of sifting through mountains of metrics across different network types, what if you had an AI-powered tool that could display all the necessary insights in an easy-to-understand format?