Operations | Monitoring | ITSM | DevOps | Cloud
Latest News
Ivanti Insights Episode 3: In the World of Privacy, Nothing is Free - Including Social Media Apps
Did you know there are currently 4.20B social media users globally? That’s 53% of the total global population! From the most popular social media platforms like Facebook and YouTube, to the hottest up and coming platforms like TikTok and Clubhouse, there is one thing they all have in common: privacy regulations and considerations should be and need to be top priority. Ivanti’s Sr.
From the SecOps Kitchen: Why Operators of Essentials Services Need to Prepare Now
Hey there, The European Union Agency for Cybersecurity (ENISA) has recently published its NIS Investment report - a survey conducted on European organisations identified as Operator of Essentials Services (OES) and Digital Service Providers (DSP).
As Funding Cuts Arrive, Can CDM Deliver on the Value of Its Promises?
For anyone who works in cybersecurity, getting a tough job done with severely limited resources is all in a day’s work. But when funding allocations suddenly shift after essential programs are already under development, it can be hard for even the most creative, resilient CIOs and CISOs to keep up.
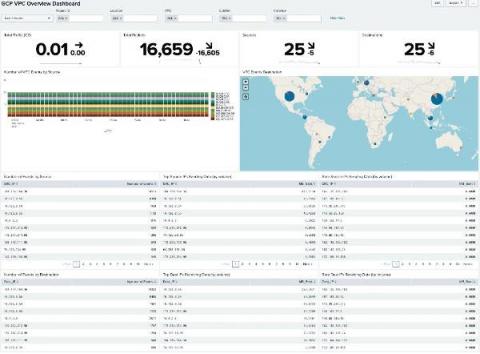
Exploring the Value of your Google Cloud Logs and Metrics
With our ability to ingest GCP logs and metrics into Splunk and Splunk Infrastructure Monitoring, there’s never been a better time to start driving value out of your GCP data. We’ve already started to explore this with the great blog from Matt here: Getting to Know Google Cloud Audit Logs. Expanding on this, there’s now a pre-built set of dashboards available in a Splunkbase App: GCP Application Template for Splunk!
The Complete Guide to Data Breach Insurance
It’s been noted that there are two types of organizations – those that have suffered a data breach, and those that will fall victim to a data breach sooner than later (most likely sooner). The hard truth of this statement is reflected in the fact that according to some sources 97% of networks will experience a security compromise over any given six-month period. And with a staggering 9.7 billion data records having been breached since 2013, these numbers are only rising.
Upgrade Better, Faster, Stronger
Imagine a Passwordless World: Is it Possible?
Imagine a world of passwordless authentication, where users anywhere on any device can become automatically validated before access is granted. Or what if I told you the phrase ‘enabling secure access effortlessly’ is what we do here at Ivanti? You might ask how.
Automating With Splunk Phantom: How Norlys Does It
Some tasks are better off automated. Paying bills on time? Automated payments. Orchestrating a coordinated response to security alerts and triaging security events? There’s Splunk Phantom for that. Monotonous tasks, in our work and personal lives, should and can be automated in order to free up time and energy to focus on the things that matter.
Five worthy reads: Are we ready for a passwordless future?
Five worthy reads is a regular column on five noteworthy items we’ve discovered while researching trending and timeless topics. This week, we explore the possibilities and challenges of a passwordless era.