Operations | Monitoring | ITSM | DevOps | Cloud
Latest News
CFEngine 3.18 LTS released - Extensibility
Today, we are pleased to announce the release of CFEngine 3.18.0! The focus of this new version has been extensibility. It also marks an important event, the beginning of the 3.18 LTS series, which will be supported for 3 years. Several new features have been added since the release of CFEngine 3.15 LTS, in the form of non-LTS releases. In this blog post we’ll primarily focus on what is new in 3.18, but we will also highlight some things released in 3.16 and 3.17.
Practical CPU time performance tuning for security software: Part 1
Software performance issues come in all shapes and sizes. Therefore, performance tuning includes many aspects and subareas, and has to adopt a broad range of methodologies and techniques. Despite all this, time is one of the most critical measurements of software performance. In this multi-part series, I’ll focus on a few of the time-related aspects of software performance — particularly for security software.
Understanding the DoD's Data Strategy: Part 2
Published in late 2020, the DoD Data Strategy emphasizes the importance of unlocking and operationalizing data-value from across its enterprise to support mission operations and maintain battlefield advantage. The strategy highlights seven goals and objectives that the DoD believes will align the DoD's Data Strategy with industry best practices.
Everything You Should Know About Spam Filters
We are all aware of the spam folder in our email dashboard. This article deals with how spam filters automatically identify and divert spam mail from our inbox to the spam folder. Spam filters are used to screen inbound emails (the emails entering a particular network) and outbound emails (the emails leaving the network). The Internet Service Providers utilize both methods for protecting the receiver and the sender. There are many types of spam filtering solutions available.
The Visibility Gap: How to Avoid Blind Spots in IT Monitoring
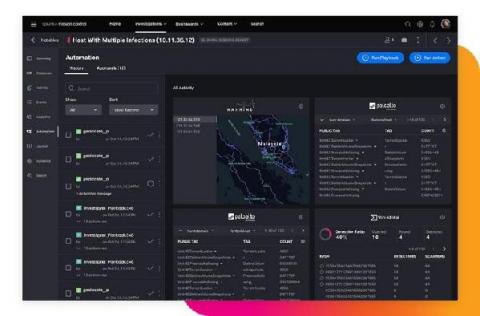
SOARing to the Clouds with Splunk SOAR
For years, security practitioners have kicked and screamed about their reality. There are too many alerts to fully investigate and manually resolve every day. There is a massive talent shortage of qualified security professionals across the globe. Then couple that with analyst burnout and siloed security point-products. All of these factors are preventing security operation centers (SOCs) from operating at their full potential, with increased efficiency, performance and speed.
Introducing the World's First Modern Cloud-Based SecOps Platform: Splunk Security Cloud
To say that the past year presented its fair share of cybersecurity challenges to the InfoSec community would be a drastic understatement. The rapid migration to remote work at scale left 80% of CIOs unprepared, and SecOps teams struggled to confront the evolving threat landscape with disparate toolkits and skill sets. Not to mention that as more organizations shifted to hybrid and multi-cloud environments at scale, cloud complexity (and cloud-based threats) skyrocketed.
Top vulnerability assessment and management best practices
By implementing these vulnerability assessment and vulnerability management best practices you will reduce the attack surface of your infrastructure. We’re human, and many things we build aren’t perfect. That’s why we take our cars for a periodic inspection, or why we have organizations certifying that products are safe to use. Software is no different.
How Biden's Executive Order on Improving Cybersecurity Will Impact Your Systems
President Joe Biden recently signed an executive order which made adhering to cybersecurity standards a legal requirement for federal departments and agencies. The move was not a surprise. It comes after a string of high-profile cyber-attacks and data breaches in 2020 and 2021. The frequency and scale of these events exposed a clear culture of lax cybersecurity practices throughout both the public and private sectors.