Operations | Monitoring | ITSM | DevOps | Cloud
%term
PagerDuty Summit 2018 - Opening Keynote
How to Troubleshoot the 33+ Stages of the Citrix Logon Process
Troubleshooting Citrix XenApp and XenDesktop logon duration is challenging because it’s a complex process, it’s asynchronous, meaning multiple things are happening simultaneously, and it’s also variable. Some logons will have 33 sub-steps in the process, and others will have more than 50. Any technology that doesn’t offer visibility into all the sub stages can only show that there is a general problem and not the true root cause of the issue.
Disable Unused IAM Access Keys Action
According to Best Practices for Managing AWS Access Keys, if you must utilize IAM access keys, it is best to remove or disable unused keys. This will close possible security holes in your AWS account. Today, we’re happy to announce a new action to help with this task: Disable Unused IAM Access Keys. This new action will iterate through the IAM users in your AWS account, determine when any access keys were last used, and if they were not used inside a configurable threshold, disable the keys.
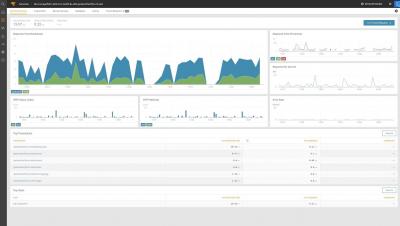
Getting started with Analytics Plus
SolarWinds Application Performance Monitor Overview
Top 3 Citrix Mistakes, Fixes and Tips - How to Become a Citrix Hero
Citrix deployments – needless to say but let me say it nevertheless – are complicated. There are too many moving parts, various dependencies, and myriad configurations and customizations. Ultimately, organizations expect seamless connectivity and access to virtualized applications and desktops for their employees and partners whenever and wherever.
Real-Time Operations Maturity: How Businesses Can Thrive in the Digital Era
It’s rare to find a business today that doesn’t rely on digital technologies and services. Retail is one example: Whether customers are buying online or in store, completing a transaction requires a website or point-of-sale system. The entire supply chain relies on IT services to deliver goods on time, to the right locations, and just like any company today, every department —from development and marketing, to HR and business services—has a critical tech stack.
Let's talk about Data Center Monitoring
The term Data Center Monitoring is used in the communications plan of some companies as if it were a product specially designed for this area. However, when it comes to these ideas we believe that they actually refer to a summary of monitoring tools facilities that are intended to support the work of Data Centre managers.
Machine Learning in IT & Digital Operations: Why Now, And What to Keep in Mind
You’ve just recovered from a critical application outage and your team is being asked to report on root cause and recommended remediation steps later this afternoon. Can you quickly analyze all the data, identify all the leading events, and discern which one was responsible for the cascading failure?