Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Cloud monitoring, security and related technologies.
Building Slack Bots for Fun: A Serverless Release Gong
We have a running joke at Stackery regarding our tiny little gong that’s used to mark the occasion when we get a new customer. And while I’m all about the sales team celebrating their successes (albeit with a far-too-small gong), I felt like the dev team needed its own way to commemorate major product releases and iterations.
Using t2.unlimited to Increase Packet Limitations
I set out to find a credit mechanism or hard-coded limit in packets per second in AWS EC2. After all my findings set out in this series so far, I had one more test to perform around t2.unlimited. I wanted to see how “unlimited” it is and the difference it makes in packet throughput on capable instance types. This post is about my findings.
Kubernetes: Securing Hybrid and Multi-Cloud Environments
AWS GuardDuty Monitoring with Logz.io Security Analytics and the ELK Stack
Last month, we announced Logz.io Security Analytics — a security app built on top of the ELK Stack, offering out-of-the-box security features such as threat intelligence, correlation, and premade integrations and dashboards. In this article, I’d like to show an example of using both the ELK Stack and Logz.io Security Analytics to secure an AWS environment.
Datadog's AWS re:Invent 2018 guide
Each November, AWS re:Invent draws thousands of AWS staff, partners, and users to Las Vegas for an intense week featuring all things AWS and AWS-related. As always, Datadog will be there and we’d love to meet you in person. Our engineers are excited to show off the new features they’ve been building and to answer your monitoring questions!
AWS ReInvent: Serverless, Stackery, and Corey Quinn of LastWeekInAWS
Welcome savvy builder. If you’ve made it to our corner of the Internet and headed to re:invent, you are in the right place. We want you to leave Las Vegas with the savvy to choose how and when to apply the growing menu of serverless capabilities to your initiatives. To help you, we’re sending our serverless-first engineers to Las Vegas with three goals.
PPS Spike Every 110 Seconds on AWS EC2
I don’t know what to say about this post… I found something weird while investigating PPS on EC2. It seems to correlate with CPU credits on t1/t2/t3 instances, but is consistently inconsistent in presentation. It only shows up when you track the stats yourself, because Cloudwatch doesn’t show the 1-second granularity needed to see these numbers.
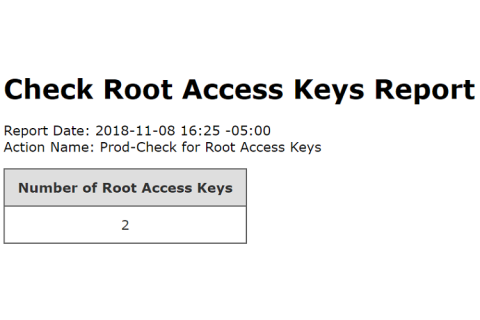
Check Root Access Keys Action
Still referencing Best Practices for Managing AWS Access Keys, best practices recommends that root access keys are never used and should be completely removed from your AWS account. Instead, IAM users with limited permissions should be used. In fact, Skeddly even prevents root access keys from being registered with Skeddly. We always recommend using IAM third-party roles, however, access keys can still be used. And we only allow IAM user access keys to be registered.
Payload Size and Max PPS on AWS EC2 - No Effect
While benchmarking packets per second (PPS) in AWS EC2 and searching for hard-coded or other software-based limitations, my early findings suggested that there definitely was a credit mechanism, complete with network throttling, in place. I now know that to be false, since finding the guaranteed throughput / best effort mechanic.