Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Containers, Kubernetes, Docker and related technologies.
Rancher as your Kubernetes application platform
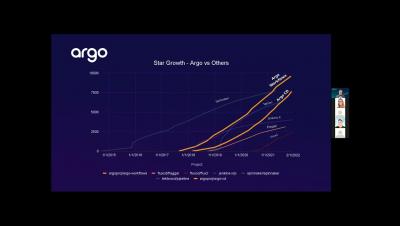
Using GitOps, Multiple Argo Instances, and Environments with Argo CD at Scale
As open-source software evolves and grows, it’s important that organizations, both large and small, can scale to keep up with their end user’s needs. At Codefresh, we are announcing a new release of our platform, Codefresh Software Delivery Platform, powered by Argo (CSDP) which delivers a scalable deployment management platform with Argo. Some of the major new features include the following support: These are some of the major new features in Codefresh’s new platform.
Using Codefresh Workflows for GitOps deployments
One of the major components of the Codefresh Software Delivery Platform is the Workflows capability that allows you to define any kind of software process for creating artifacts, running unit tests, running security scans, and all other actions that are typically used in Continuous Integration (CI). At first glance, Codefresh Workflows might look like the typical pipelines that you would find in any popular CI product but if you look under the hood you will realize looks can be deceiving.
Introducing Codefresh Software Delivery Platform, Powered by Argo
Delivering new software is the single most important function of businesses trying to compete today. Many companies get stuck with flaky scripting, manual interventions, complex processes, and large unreliable tool stacks across diverse infrastructure. Software teams are left scrambling to understand their software supply chain and discover the root cause of failures. It’s time for a new approach.
The Top 7 Open Source Tools for Securing Your Kubernetes Cluster
This article explores how to secure production Kubernetes clusters with the help of open source tools. As a prerequisite, you’ll need to have basic beginner-level knowledge of Docker and Kubernetes. In a nutshell, Kubernetes is a container orchestration tool and Docker is a containerization platform. Some of the most famous Kubernetes clusters managed by cloud providers include AWS EKS, Azure AKS, and Google CKE.
Containerization and Kubernetes Monitoring
Tutorial: Auto-instrumentation of a Java app by OpenTelemetry for K8s Environment
Introducing our exciting new ambassador program: Calico Big Cats
The Project Calico community is one of the most collaborative and supportive communities in the open-source space. Our community has shown great engagement through the years, which has helped us maintain and grow the project. Thanks to our 200+ contributors from all over the world, Calico Open Source (the solution born out of the project) is powering 1.5M+ nodes daily across 166 countries.