Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on DevOps, CI/CD, Automation and related technologies.
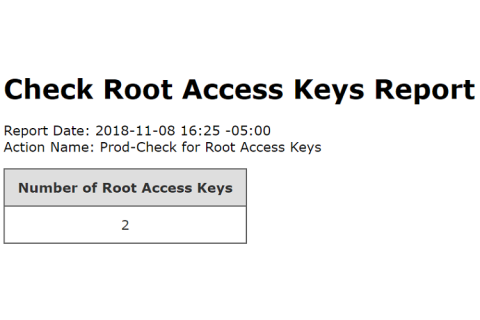
Check Root Access Keys Action
Still referencing Best Practices for Managing AWS Access Keys, best practices recommends that root access keys are never used and should be completely removed from your AWS account. Instead, IAM users with limited permissions should be used. In fact, Skeddly even prevents root access keys from being registered with Skeddly. We always recommend using IAM third-party roles, however, access keys can still be used. And we only allow IAM user access keys to be registered.
Observability-Driven Development
Payload Size and Max PPS on AWS EC2 - No Effect
While benchmarking packets per second (PPS) in AWS EC2 and searching for hard-coded or other software-based limitations, my early findings suggested that there definitely was a credit mechanism, complete with network throttling, in place. I now know that to be false, since finding the guaranteed throughput / best effort mechanic.
Disable Unused IAM Access Keys Action
According to Best Practices for Managing AWS Access Keys, if you must utilize IAM access keys, it is best to remove or disable unused keys. This will close possible security holes in your AWS account. Today, we’re happy to announce a new action to help with this task: Disable Unused IAM Access Keys. This new action will iterate through the IAM users in your AWS account, determine when any access keys were last used, and if they were not used inside a configurable threshold, disable the keys.
Near Real-Time Log Collection From Amazon S3 Storage
We are very excited to announce a new capability for our Amazon S3 sources. Until recently, the only method Sumo Logic used for discovering new data in an S3 bucket was periodic polling. However, with our new notification-based approach, users can now configure S3 sources such that Sumo Logic is notified immediately (via AWS SNS) whenever a new item is added to an S3 bucket, eliminating the need to wait for new objects to be discovered via periodic polling.
Logs for Dogs: Automating Infrastructure, Scaling, Deployment, Logging and Alerting at Wag!
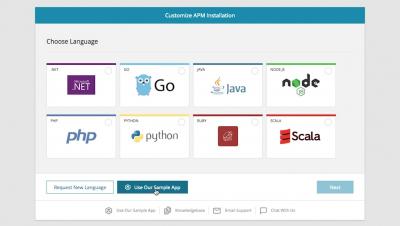
How to Install a Docker Sample Application in SolarWinds AppOptics
An in-depth look at 100% Zero Downtime deployments with Terraform
At Checkly, we run our browser checks on AWS EC2 instances managed by Terraform. When shipping a new version, we don’t want to interrupt our service, so we need zero downtime deployments. Hashicorp has their own write up on zero downtime upgrades, but it only introduces the Terraform configuration without any context, workflow or other details that are needed to actually make this work in real life™.
Using JFrog Artifactory as Docker Image Repository
This article is a continuation of Deploying JFrog Artifactory with Rancher. In this chapter we'll demonstrate how to use JFrog Artifactory as a private repository for your own Docker images.