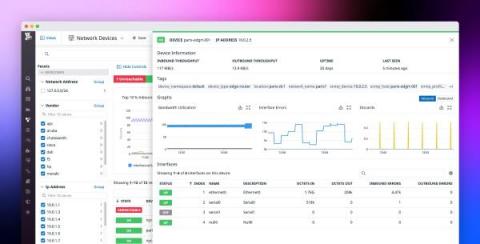
Extend your Datadog functionality with Datadog Apps
Last year, we launched the Datadog Marketplace, which lets Datadog partners develop and trade applications that provide custom monitoring solutions for specific use cases. Now, we’re pleased to announce Datadog Apps, which introduces even further customizability to the Datadog platform. With Datadog Apps, you can now build and share your own Datadog UI features that seamlessly combine functionality from your third-party tools with the full range of Datadog’s monitoring capabilities.