Top 8 uses of cloud computing
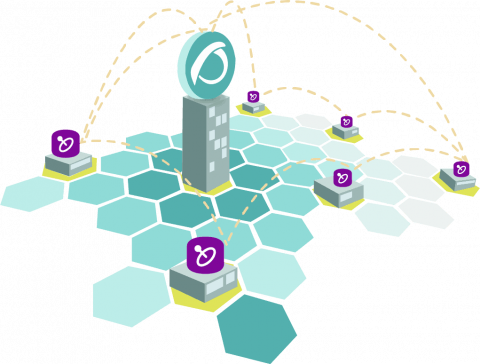
The cloud is gaining widespread adoption. For many organizations, cloud computing has become an indispensable tool for communication and collaboration across distributed teams. Whether you are on Amazon Web Services (AWS), Google Cloud, or Azure. the cloud can reduce costs, increase flexibility, and optimize resources. If you have spent your career in buzzing server rooms full of cable nests, you may be wondering what all the fuss is about.