Operations | Monitoring | ITSM | DevOps | Cloud
The Increasing Popularity of Ransomware Amongst Cybercriminals
Cybercriminals are becoming increasingly savvy and ransomware attacks have soared over the last decade. A recent PwC UK Cyber Threat Intelligence report revealed a spike in cybersecurity incidents which have significantly affected many organisations that are already dealing with challenges caused by the pandemic.
Easily ingest data to Elastic via Splunk
As organizations migrate to Elastic from incumbent vendors, quickly onboarding log data from their current solution into Elastic is one of the first orders of business. Data onboarding often involves having to adjust ingestion architecture and implement configuration changes across data sources. We want to ensure that users trialing or migrating to Elastic can get data in quickly to start seeing the power of Elastic solutions as quickly as possible.
New in Kibana: How we made it easier to manage visualizations and build dashboards
Our Kibana team has been hard at work implementing and executing on a new Kibana strategic vision to streamline the dashboard creation process and sand down the rough edges of creating visualizations for dashboards. We accomplished our goal and reduced the overall time it takes users to go from a blank slate to a meaningful dashboard that conveys insights about the data.
Why Dashboards Are Not Enough to Proactively Monitor Your Business
How much is your company losing by reacting to problems after they’ve had a negative impact on your bottom line? How many customers churn in the time it takes you to notice complaints to your call center? Proactive business monitoring allows you to detect incidents before they have a negative impact on your company’s revenue and reputation.
Red Canary says 43% Lack Readiness to Notify Customers of a Security Breach
Unify Visibility Across Your Monitoring Tools with DX Operational Intelligence
For today’s businesses, there’s a premium on delivering innovative user experiences. As a result, stakes continue to grow for the teams in charge of supporting new digital experiences. To successfully implement modern delivery chains, IT operations need to establish comprehensive coverage that delivers unified visibility of the entire enterprise ecosystem. They need observability that spans from mobile applications to networks and mainframes.
Splunk Workload Pricing For the Win!
We at Splunk know that data drives better decisions. We see this with customers, and we live it every day in our own operations within Splunk. Running large cloud services across multiple cloud providers, we have to manage data policies and data processing needs against an increasing set of use cases, as well as the backdrop of regulatory, privacy and security frameworks.
Using pre-built Monitors to proactively monitor your application infrastructure
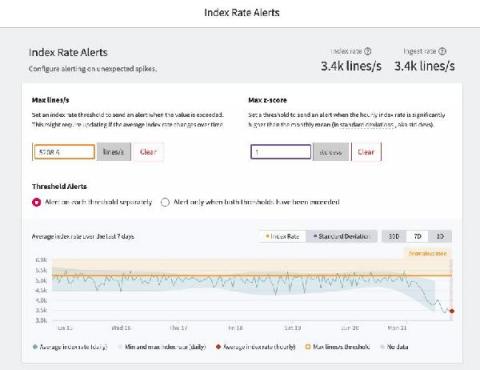
The Spike Protection Bundle with Index Rate Alerting
For DevOps teams that want to accelerate release velocity and improve reliability, logs can unlock the insights you need to move faster. But for managers and budget owners, logging can be an unpredictable pain. Trying to estimate logging spend, especially with the adoption of microservices and container-based architecture, seems like an impossible task.