Operations | Monitoring | ITSM | DevOps | Cloud
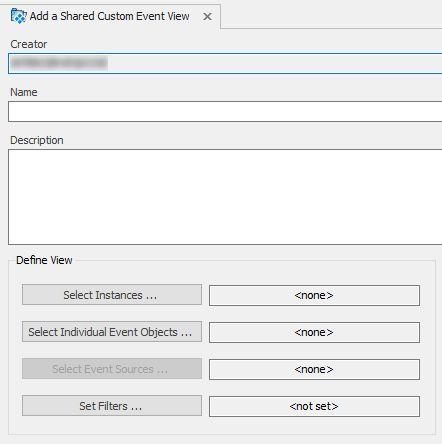
Creating Custom Event Views in SQL Sentry
How to monitor containerized Kafka with Elastic Observability
Kafka is a distributed, highly available event streaming platform which can be run on bare metal, virtualized, containerized, or as a managed service. At its heart, Kafka is a publish/subscribe (or pub/sub) system, which provides a "broker" to dole out events. Publishers post events to topics, and consumers subscribe to topics. When a new event is sent to a topic, consumers that subscribe to the topic will receive a new event notification.
Consumer broadband takes center stage - are CSPs ready?
It could be argued that consumer broadband networks have historically been poor neighbours of business networks, with CSPs investing more funds in providing better SLAs to their higher paying business customers. But like it did for many of our pre-set ideas, the pandemic turned the tables around for broadband priority. Forced work from home policies, remote learning, and quarantines have effectively turned consumer broadband into business/educational/health broadband services for many.
Coffee Break Webinar Series: Intelligent Observability for IT Ops
IT Operations teams are often the bedrock of the digital business, ensuring that processes and services continue humming smoothly as developers continue to evolve and increase customer value. But increasingly complex systems can flood them with alerts that get in the way of operators from doing their best work and paving the way for new, innovative services.
Analytics-Based Investigation and Automated Response with AWS + Splunk Security Solutions
Organizations are migrating an increasing amount of their infrastructure into the cloud. The cloud provides organizations with a number of benefits like greater scalability, improved reliability and faster time to value. However, these potential benefits can be offset if security is an afterthought.
The Importance of Network Documentation
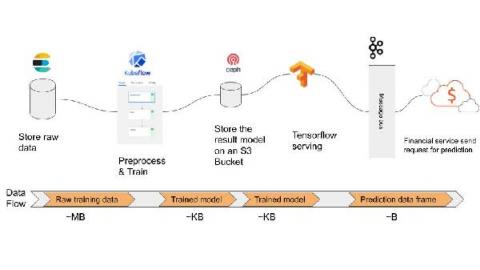
AI on premise: benefits and a predictive-modeling use case
Running an Artificial Intelligence (AI) infrastructure on premise has major challenges like high capex and requires internal expertise. It can provide a lot of benefits for organisations that want to establish an AI strategy. The solution outlined in this post illustrates the power and the utility of the universal Operator Lifecycle Manager (OLM) using Juju, a universal OLM, to create and manage on premise AI infrastructure.
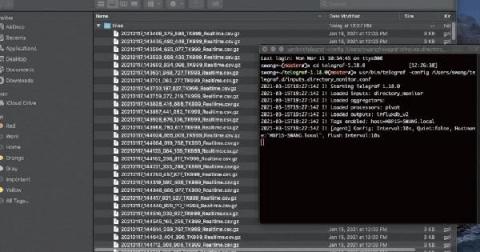
New in Telegraf 1.18.0: Beat, Directory, NFS, XML, Sensu, SignalFX and More!
Last week we released Telegraf 1.18 with a range of new plugins including Elastic Beats, directory monitoring, NFS, XML parsing and some aggregators and processors to help with your data ingestion. All of these packages were written in Go 1.16.2. This was one of our largest releases in a while and couldn’t have been done without the 70+ Telegraf community members who contributed to writing plugins, fixing bugs, reviewing code, and everything else to improve Telegraf!
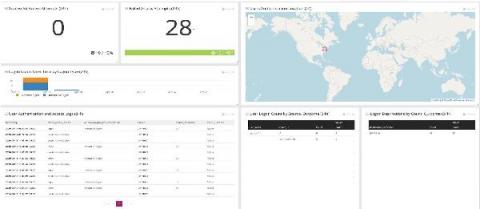
Monitoring Logs for Insider Threats During Turbulent Times
For logs and tracking insider threats, you need to start with the relevant data. In these turbulent times, IT teams leverage centralized log management solutions for making decisions. As the challenges change, the way you’re monitoring logs for insider threats needs to change too. Furloughs, workforce reductions, and business practice changes as part of the COVID stay-at-home mandates impacted IT teams.