Operations | Monitoring | ITSM | DevOps | Cloud
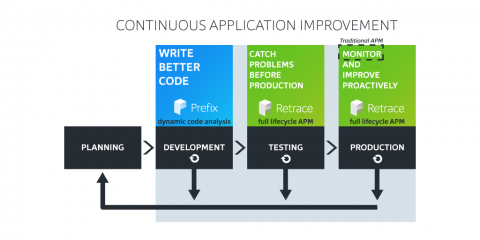
What is Continuous Application Improvement?
CAI stands for Continuous Application Improvement. It is a software improvement process that is implemented at each step of the SDLC, ensuring immediate feedback at each step rather than waiting till risk levels and impact has gone up. When you implement CAI you shift your improvement process as far left as possible and you catch software bugs and performance problems where they are introduced, eliminating countless hours of time spent chasing issues.
The Ultimate List of Digital Employee Experience Job Titles
Job titles are in constant flux these days, especially in the world of IT. While some can border on the bizarre and ambiguous (thinking of you, Mr. “Digital Sherpa” and “Software Ninja”) most titles reveal very specific clues about the nature of modern work and the changing demands of business. In the last few years, large enterprise companies have realized their digital employee experience is just as important as their digital customer experience.
Improving Kubernetes Clusters' Efficiency with Log Management
Log management plays an important role in helping to debug Kubernetes clusters, improve their efficiency, and monitor them for any suspicious activity. Kubernetes is an open-source cluster management software designed for the deployment, scaling, and operations of containerized applications.
Serverless is more than AWS Lambda
Too often serverless is equated with just AWS Lambda. Yes, it’s true: Amazon Web Services (AWS) helped to pioneer what is commonly referred to as serverless today with AWS Lambda, which was first announced back in 2015. But in 2020, it’s important for enterprises to understand that the serverless landscape is much bigger with more opportunities. Serverless is sometimes (narrowly) defined as just being about functions-as-a-service, but that’s a very limited viewpoint.
Power of CMDB in IT Digital Transformation
Whether we’re creating or managing on the fly with microservices, serverless compute, or containerization and APIs, digital rules everything around us. From IT operations, service delivery and asset management to even the fundamental makeup of our company’s core products and services, it’s all gone—or going—to the cloud.
Gen Z are here - and they're swiping, tapping and snapping Australian workplaces into a new era
Let’s assume that the average Australian university graduate enters the workforce somewhere between the ages of 21 and 24, bringing with them a qualification (or two, or three), a fierce determination to establish a secure career, and a finely-tuned radar for what’s authentic and what’s fake news.
How 5G can pave the way for emerging technologies
From the discovery of fire to the development of the internet, society’s need to communicate and live as a social unit has inspired endless innovation. Soon we'll be witness to the pinnacle of wireless technology: fifth-generation wireless networks (5G). By allowing users to communicate and share data at breakneck speed, 5G could prove to be a paradigm shift in information consumption and sharing.
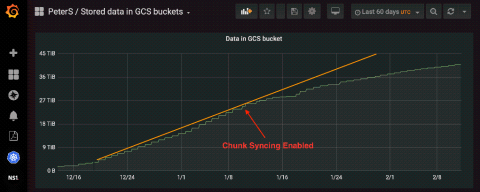
How Loki Reduces Log Storage
Several months ago, Bryan Boreham introduced a few changes to Cortex that massively reduced its storage requirements. The changes were quite simple and altogether had a nice benefit of using almost 3x less data storage than prior versions. Since Loki shares a lot of code with Cortex, could we use these ideas to the same effect? (Spoiler alert: Yes, we can!)
How to Monitor Your Host Metrics Automatically
Today, we’ll dive deep into monitoring hosts. The good news is that we’ll point you to some shortcuts on how to set up host monitoring in an easy way. The bad news is that we won’t be doing any percussive maintenance on any host. To monitor hosts, you have to set a few layers in place. Doing all this by yourself would be the hard way. You may ask: “How hard could it be?”.