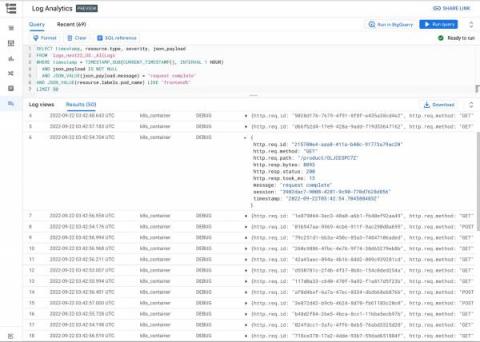
Why You Need Synthetic Monitoring
Synthetic monitoring can be one of the most powerful tools in your DevOps team’s toolkit, especially for the SRE, yet is one that is often overlooked by people building out a reliability mindset. Synthetic monitoring permits you to simulate any transaction or interaction users can have in your website or app, from places around the world, as often as you’d like.