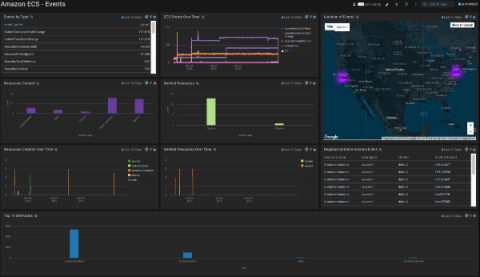
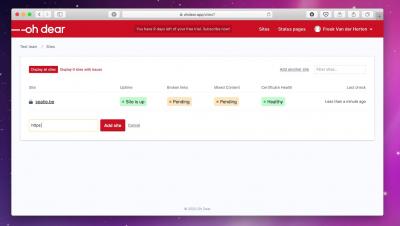
Monitoring critical business applications while working remotely
With a huge number of employees around the globe working remotely during the COVID-19 pandemic, delivering uninterrupted business services to customers has become a major challenge. This requires strict monitoring of all critical business applications in order to accommodate an increased amount of requests, which can cause a critical downtime if not monitored appropriately.