Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on IT Networks and related technologies.
How to Detect Network Congestion | Obkio
Application Discovery with DX Unified Infrastructure Management
Having any form of application discovery can be of great benefit. With these capabilities, you can determine what is deployed within your infrastructure and better understand what monitoring to apply to each device. When you know which applications are running within your environment, you can group devices by their associated applications.
Jitter vs Latency - What are the Differences and Why Those Things Matter
The jitter and latency are the characteristics related to the flow in the application layer. Jitter and latency are the metrics used to assess the network's performance. The major distinction between jitter and latency is that latency is defined as a delay via the network, whereas jitter is defined as a change in the amount of latency. Increases in jitter and latency have a negative impact on network performance, therefore it's critical to monitor them regularly.
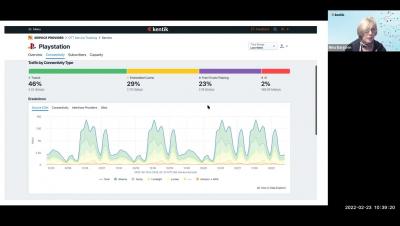
Use Data to Dig into ISP Networks
Predict the cost of IP ranges with new enhancements to the Resources tab
One of our most requested and popular features, IP ranges for the Docker executor, recently became available to all customers on a Performance or Scale plan. With IP ranges, you can route job traffic through an IP address that is verifiably associated with CircleCI. This enables your team to meet compliance requirements by limiting the connections that communicate with your infrastructure. With any new feature, you want to know how much it’s going to cost your team.
Zero Trust Network Access (ZTNA) vs VPN: the core evolution
According to Gartner, by 2023, 60% of enterprises will phase out their VPN in favor of Zero Trust Network Access (ZTNA). In this blog, discover the four key advantages of ZTNA vs VPN. VPN (Virtual Private Network) has been the dominant solution securing remote access for users and has been considered a good solution for almost three decades. VPN benefits included keeping data secure, protecting online privacy, and reducing bandwidth throttling.
Keeping Federal and Local Government Networks Safe Through Monitoring
It is always big news when governmental organizations are attacked. And they are attacked frequently. Hackers love headlines, which is one reason to go after high profile government targets. But the real reason hackers love governmental organizations is because that’s where the juicy data is. Even small governmental organizations hold confidential and classified information—exactly the secrets state-sponsored groups and other cybercriminals drool over.