Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Security Observability - Vulnerability Dashboard and Risk Scorecard
Streamlining SAP Kernel upgrades with Avantra
Picture the SAP Kernel as the heartbeat of the system, vitalizing the core programs upon which the fundamental functionality of SAP applications rely on. It's the life force pulsing through the application server, executable programs, database, and operating system, rather than merely encompassing them within itself. SAP Kernel upgrades refer to updating the system's current executables with upgraded versions. These upgrades are essential to patch security vulnerabilities and fix bugs. Besides bug fixing, SAP Kernel upgrades improve hardware compatibility, boost speed, and enhance stability.
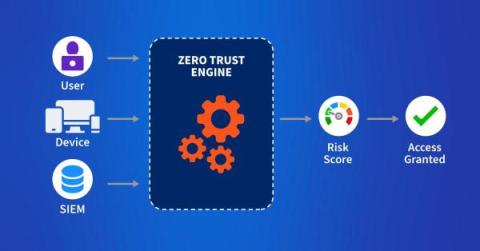
Security Webinar, Zero Trust For Users
Fighting DDoS at the Source
Death, Taxes and Phishing - Cybersecurity Research Results (Pt. 1) | Ep.33 Security Insights Podcast
How to Harden Zero-Trust Cloud Network Policy with Kentik
Zero trust in the cloud is no longer a luxury in the modern digital age but an absolute necessity. Learn how Kentik secures cloud workloads with actionable views of inbound, outbound, and denied traffic.
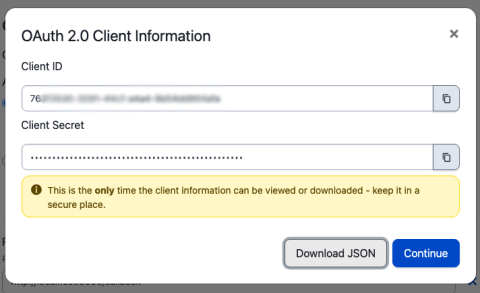
Build Sophisticated Apps for Your PagerDuty Environment Using OAuth 2.0 and API Scopes
Many PagerDuty customers create their own apps to help them manage their PagerDuty environments. Teams might have any number of workflows that might benefit from a custom application. A PagerDuty admin might want to be able to load CSV files with new users and their contact information into PagerDuty when new teams join the platform, or load new services before they are released to production.
The DevOps Security and Compliance Guide
The fast-paced nature of modern software development means developers are capable of deploying changes to production multiple times a day. But, while DevOps allows development teams to deliver new features faster, increased deployment frequency can make it more difficult to stay on top of security threats. It only takes one malicious or incompetent change to dramatically increase the risk exposure of an application.