Operations | Monitoring | ITSM | DevOps | Cloud
SolarWinds Lab Bits: Insights Into the 2020.2 Release for SolarWinds IT Security Products
SolarWinds Lab Bits: 2020.2 Network Management Solution Updates
Getting up and running with Calico Enterprise on EKS
Fastest News: Best Performing News Website
News teams often compete to break the story first. We think they should also compete on being the first to load their website. Let’s apply our web performance skills to a real world example: which news website has the best performance? Let’s solve this question by loading the homepages of some large news sites. A sampling of Alexa’s Top Sites gives four test candidates: Google News, CNN, The New York Times (NYT), and Fox News. Take a look, which feels fastest to you?
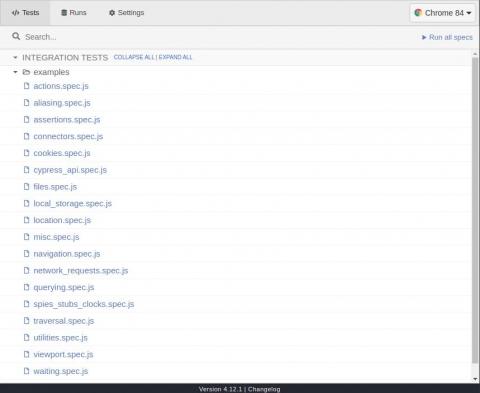
Modern ways of end-to-end testing with Cypress JS
The ultimate goal of writing tests should be improving the user’s in-app experience and increasing developers’ confidence in shipping new or improved apps. The Mattermost team has been continuously writing different types of tests to improve the product. Such extensive automated testing has enabled them to ship a new release—with new features and improvements—every single month for the last few years. Thousands of developers contribute to the codebase.
Service Level Management: Tying it Together With SLAs, SLOs, and XLAs
Create Custom Icinga Powershell Modules and Plugins
Today I will show you briefly how to build your own Powershell Modules/Plugins using icinga-powershell-framework. As you might know, we recently started writing plugins in Powershell that can be used to monitor windows-services in Icinga2 in a simple way. If you are interested in learning more about it, everything is documented here down to the smallest detail.
Introduction to Windows tokens for security practitioners
This blog series is aimed at giving defense practitioners a thorough understanding of Windows access tokens for the purposes of detection engineering. Here in Part 1, we'll cover key concepts in Windows Security. The desired outcome is to help defenders understand how access tokens work in Windows environments.
Security operations: Cloud monitoring and detection with Elastic Security
As many organizations have migrated their infrastructure, applications, and data to cloud offerings, adversaries have extended their operational capabilities in cloud environments to achieve their mission — whether that means stealing intellectual property, disrupting business operations, or holding an organization’s data for ransom.